PayPal
Informations concernant votre compte:
Dans le cadre de nos mesures de sécurité, Nous vérifions régulièrement l'activité de l'écran PayPal. Nous avons demandé des informations à vous pour la raison suivante:
Notre système a détecté des charges inhabituelles à une carte de crédit liée à votre compte PayPal.
Numéro de Référence: PP-259-187-991
C'est le dernier rappel pour vous connecter à PayPal, le plus tôt possible. Une fois que vous serez connecter. PayPal vous fournira des mesures pour rétablir l'accès à votre compte.
une fois connecté, suivez les étapes pour activer votre compte . Nous vous remercions de votre compréhension pendant que nous travaillons à assurer la sécurité compte.
Cliquer ici pour vérifier votre compte
Nous vous remercions de votre grande attention à cette question. S’il vous plaît comprenez que c'est une mesure de sécurité destinée à vous protéger ainsi que votre compte. Nous nous excusons pour tout inconvénient..
Département de revue des comptes PayPal
Copyright © 2017 PayPal. Tous droits réservés.
PayPal (Europe) S.à r.l. & Cie, S.C.A. Société en Commandite par
Actions Siège social : 5ème étage 22-24 Boulevard Royal L-2449,
Luxembourg RCS Luxembourg B 118 349
Email PayPal n° PP059
Protégez votre compte
Assurez-vous de ne jamais donner votre mot de passe pour les sites Web frauduleux.
Toute sécurité d'accès au site PayPal ou à votre compte, ouvrez une fenêtre de navigateur Web (Internet Explorer ou Netscape) et tapez dans la page de connexion de PayPal (http://paypal.fr/) afin de vous assurer que vous êtes sur le véritable PayPal Site.
Pour plus d'informations sur la protection contre la fraude, s’il vous plaît consulter nos conseils de sécurité
Protégez votre mot de passe
Vous ne devriez jamais donner votre mot de passe PayPal à personne.
Phishing screenshot :
Email analysis :
NOTE : Paypal@contact.ca
NOTE : Received : from User ([105.73.26.254])
NOTE : by mail.xinyiglass.com with Microsoft SMTPSVC(6.0.3790.3959);
Phishing analysis :
CLICK : Cliquer ici pour vérifier votre compte
OPEN : http://lelogisbranche.fr/js/mage/adminhtml/wysiwyg/tiny_mce/plugins/magentovariable/img/Notification-servier-compte-demande.php
REDIRECT : http://www.sagarparaptti.org.in/cgi-sys/suspendedpage.cgi
NOTE : Phishing was removed.
Tuesday, July 11, 2017
Thursday, June 1, 2017
Рiԁ:382663110 (Apple Phishing)
myApple
Apple
Hello *@*,
We have unfortunately been unable to review some information in your Profile. To confirm your details Continue and SignOn.
Continue and Sign On
With our respects,
Apple Team
You're receiving this email from us because this address was entered to sign at apple.com. Having trouble? Let us know here.
© Copyright 2017 Apple.com
Email analysis :
NOTE : info@appleacres.co.uk
NOTE : Received : from smalldisk10 (13.65.207.162)
NOTE : by msx-van.nhc.local (192.168.101.10)
NOTE : Received : from MSX-VAN.nhc.local (192.168.101.10)
NOTE : by MSX-VAN.nhc.local (192.168.101.10)
NOTE : Received : from mail01.nhcweb.com (mail.nhcweb.com. [207.194.62.167])
Phishing analysis :
CLICK : Continue and Sign on
OPEN : http://charishospice.com/joy.php?*
REDIRECT : http://www.apple.com-logind52ac2j8rcgbjgpakeohtcy23rnbdx1vqw9o0w97rdamd89d67.saopaulonanet.com.br/apple/unitedstatesapple/*
SCREENSHOT :
Apple
Hello *@*,
We have unfortunately been unable to review some information in your Profile. To confirm your details Continue and SignOn.
Continue and Sign On
With our respects,
Apple Team
You're receiving this email from us because this address was entered to sign at apple.com. Having trouble? Let us know here.
© Copyright 2017 Apple.com
Email analysis :
NOTE : info@appleacres.co.uk
NOTE : Received : from smalldisk10 (13.65.207.162)
NOTE : by msx-van.nhc.local (192.168.101.10)
NOTE : Received : from MSX-VAN.nhc.local (192.168.101.10)
NOTE : by MSX-VAN.nhc.local (192.168.101.10)
NOTE : Received : from mail01.nhcweb.com (mail.nhcweb.com. [207.194.62.167])
Phishing analysis :
CLICK : Continue and Sign on
OPEN : http://charishospice.com/joy.php?*
REDIRECT : http://www.apple.com-logind52ac2j8rcgbjgpakeohtcy23rnbdx1vqw9o0w97rdamd89d67.saopaulonanet.com.br/apple/unitedstatesapple/*
SCREENSHOT :
Tuesday, May 30, 2017
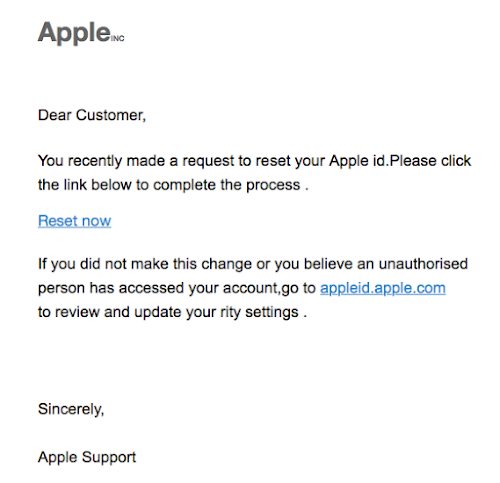
You recently made a request to reset your Apple id (Apple Phishing)
AppleINC
Dear Customer,
You recently made a request to reset your Apple id.Please click the link below to complete the process .
Reset now
If you did not make this change or you believe an unauthorised person has accessed your account,go to appleid.apple.com
to review and update your rity settings .
Sincerely,
Apple Support
Phishing screenshot :
Email analysis :
NOTE : paypal@service.fr
NOTE : Received : from lfsharedfs.FARMINDUSTRIA.LOCAL
NOTE : (extranet.farmindustria.com.pe [200.10.71.170])
Phishing analysis :
CLICK : http://amedamr06.webstarterz.com/apple.id.com
REDIRECT : http://93.182.172.19/Apple/Login.php?sslchannel=true&sessionid=*
SCREENSHOT :
Your Apple ID has been locked ! (Apple Phishing)
Validate your account information.
Dear iTunes Customer,
This is an automatic message sent by our security system to let you know that you have 48 hours to confirm your account information.
To validate your account information associated with your Apple ID, please
Visit the My Apple ID website
and sign in with your Apple ID and password. This will help protect your account in the future. This process does not take more than 3 minutes.
We apologise for any inconvenience caused.
Your sincerely,
Apple Security Department
TM and copyright 2017 Apple Inc. 1 Infinite Loop, MS 83-DM, Cupertino, CA 95014.
All Rights Reserved / Keep Informed / Privacy Policy / My Apple ID
Phishing screenshot :
Email analysis :
NOTE : noreply@email.apple.co.jp
NOTE : Received : from SERVER1 ([124.248.205.5])
Phishing analysis :
Click : Visit the My Apple ID website
OPEN : http://107.173.193.7/~eqjaeahu/index2.html
SCREENSHOT :
REDIRECT : http://107.173.193.7/~eqjaeahu/New1/*/suspended.php
SCREENSHOT :
CLICK : Confirm My Account
REDIRECT : http://107.173.193.7/~eqjaeahu/New1/*/personal.php
SCREENSHOT :
Dear iTunes Customer,
This is an automatic message sent by our security system to let you know that you have 48 hours to confirm your account information.
To validate your account information associated with your Apple ID, please
Visit the My Apple ID website
and sign in with your Apple ID and password. This will help protect your account in the future. This process does not take more than 3 minutes.
We apologise for any inconvenience caused.
Your sincerely,
Apple Security Department
TM and copyright 2017 Apple Inc. 1 Infinite Loop, MS 83-DM, Cupertino, CA 95014.
All Rights Reserved / Keep Informed / Privacy Policy / My Apple ID
Phishing screenshot :
Email analysis :
NOTE : noreply@email.apple.co.jp
NOTE : Received : from SERVER1 ([124.248.205.5])
Phishing analysis :
Click : Visit the My Apple ID website
OPEN : http://107.173.193.7/~eqjaeahu/index2.html
SCREENSHOT :
REDIRECT : http://107.173.193.7/~eqjaeahu/New1/*/suspended.php
SCREENSHOT :
CLICK : Confirm My Account
REDIRECT : http://107.173.193.7/~eqjaeahu/New1/*/personal.php
SCREENSHOT :
Tuesday, May 23, 2017
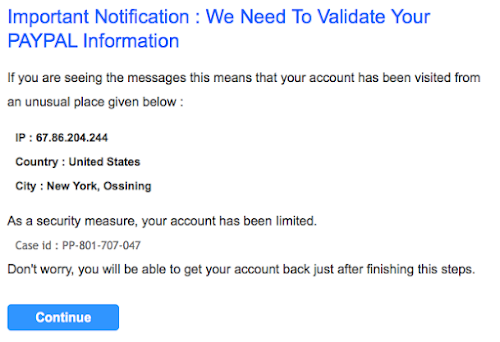
Confirme your account ! (PayPal Phishing)
Important Notification : We Need To Validate Your ΡΑΥΡΑL Information
If you are seeing the messages this means that your account has been visited from an unusual place given below :
IP : 67.86.204.244
Country : United States
City : New York, Ossining
As a security measure, your account has been Iimited.
Case id : PP-801-707-047
Don't worry, you will be able to get your account back just after finishing this steps.
Continue
Email analysis :NOTE :
NOTE : Received : from d793.dinaserver.com (d793.dinaserver.com. [82.98.157.143])
NOTE : firstsunmallorca@d793.dinaserver.com
NOTE : X-Mailer : PHPMailer (phpmailer.sourceforge.net) [version ]
NOTE : firstsunmallorca@d793.dinaserver.com designates 82.98.157.143 as permitted sender)
Phishing screenshot :
Phishing analysis :
CLICK : Continue
OPEN : https://dhartiagro.net/aspnet_client/system_web/4_0_30319/HTTPS/Myaccount/home/new/Update
REDIRECT : https://dhartiagro.net/aspnet_client/system_web/4_0_30319/HTTPS/Myaccount/home/new/Update/myaccount/signin/
NOTE : VALIDATE FORM
REDIRECT : https://dhartiagro.net/aspnet_client/system_web/4_0_30319/HTTPS/Myaccount/home/new/Update/myaccount/settings/?verify_account=session=NL&*&dispatch=*
SCREENSHOT :
If you are seeing the messages this means that your account has been visited from an unusual place given below :
IP : 67.86.204.244
Country : United States
City : New York, Ossining
As a security measure, your account has been Iimited.
Case id : PP-801-707-047
Don't worry, you will be able to get your account back just after finishing this steps.
Continue
Email analysis :NOTE :
NOTE : Received : from d793.dinaserver.com (d793.dinaserver.com. [82.98.157.143])
NOTE : firstsunmallorca@d793.dinaserver.com
NOTE : X-Mailer : PHPMailer (phpmailer.sourceforge.net) [version ]
NOTE : firstsunmallorca@d793.dinaserver.com designates 82.98.157.143 as permitted sender)
Phishing screenshot :
Phishing analysis :
CLICK : Continue
OPEN : https://dhartiagro.net/aspnet_client/system_web/4_0_30319/HTTPS/Myaccount/home/new/Update
REDIRECT : https://dhartiagro.net/aspnet_client/system_web/4_0_30319/HTTPS/Myaccount/home/new/Update/myaccount/signin/
NOTE : VALIDATE FORM
REDIRECT : https://dhartiagro.net/aspnet_client/system_web/4_0_30319/HTTPS/Myaccount/home/new/Update/myaccount/settings/?verify_account=session=NL&*&dispatch=*
SCREENSHOT :
PayPal Phishing
PayPal
Informations concernant votre compte:
Dans le cadre de nos mesures de sécurité, Nous vérifions régulièrement l'activité de l'écran PayPal. Nous avons demandé des informations à vous pour la raison suivante:
Notre système a détecté des charges inhabituelles à une carte de crédit liée à votre compte PayPal.
Numéro de Référence: PP-259-187-991
C'est le dernier rappel pour vous connecter à PayPal, le plus tôt possible. Une fois que vous serez connecter. PayPal vous fournira des mesures pour rétablir l'accès à votre compte.
une fois connecté, suivez les étapes pour activer votre compte . Nous vous remercions de votre compréhension pendant que nous travaillons à assurer la sécurité compte.
Cliquer ici pour vérifier votre compte
Nous vous remercions de votre grande attention à cette question. S’il vous plaît comprenez que c'est une mesure de sécurité destinée à vous protéger ainsi que votre compte. Nous nous excusons pour tout inconvénient..
Département de revue des comptes PayPal
Copyright © 2017 PayPal. Tous droits réservés.
PayPal (Europe) S.à r.l. & Cie, S.C.A. Société en Commandite par
Actions Siège social : 5ème étage 22-24 Boulevard Royal L-2449,
Luxembourg RCS Luxembourg B 118 349
Email PayPal n° PP059
Protégez votre compte
Assurez-vous de ne jamais donner votre mot de passe pour les sites Web frauduleux.
Toute sécurité d'accès au site PayPal ou à votre compte, ouvrez une fenêtre de navigateur Web (Internet Explorer ou Netscape) et tapez dans la page de connexion de PayPal (http://paypal.fr/) afin de vous assurer que vous êtes sur le véritable PayPal Site.
Pour plus d'informations sur la protection contre la fraude, s’il vous plaît consulter nos conseils de sécurité
Protégez votre mot de passe
Vous ne devriez jamais donner votre mot de passe PayPal à personne.
--
This email was Virus checked by Astaro Security Gateway. http://www.sophos.com
Email analysis :
NOTE : Paypal@contact.ca
NOTE : Received : from [200.107.238.35] (port=2757 helo=User) by mx1.shary.com.sa
NOTE : client-ip=94.77.230.169;
Phishing screenshot :
Phishing analysis :
CLICK : Cliquer ici pour vérifier votre compte
OPEN : http://mir-pchelovoda.ru/components/com_acepolls/views/poll/tmpl/Notifications-service-demande-compte-ca.php
REDIRECT : http://www.sunshinetravel.az/js/tinymce/plugins/autoresize/ooo412312aaaa/Notifications-compte-Canada-quebec-verified-moi-information.ca/comfirmetions-service-information-compte-demande.ca/
SCREENSHOT :
CLICK : CONNEXION
RESULT : BAD PASSWORD...
REDIRECT : http://www.sunshinetravel.az/js/tinymce/plugins/autoresize/ooo412312aaaa/Notifications-compte-Canada-quebec-verified-moi-information.ca/comfirmetions-service-information-compte-demande.ca/error.php
The website sunshinetravel was used to store this PayPal phishing :
Thursday, May 18, 2017
Please recheck your delivery address USPS parcel 632063287
Hello,
This is to confirm that your item has been shipped at Tue, 16 May 2017 10:49:00 -0700.
You can print the shipment label by clicking on the link.
information.doc
With sincere thanks.
Shanae Stovall - USPS Support Clerk.
Email analysis :
NOTE : fisou75@viajeseci.es
NOTE : Received : from viajeseci.es (unknown [222.222.219.154])
Phishing analysis :
CLICK : information.doc
OPEN : http://be-tiger.com/wp-content/sg.php
RESULT : Phishing was removed
This is to confirm that your item has been shipped at Tue, 16 May 2017 10:49:00 -0700.
You can print the shipment label by clicking on the link.
information.doc
With sincere thanks.
Shanae Stovall - USPS Support Clerk.
Email analysis :
NOTE : fisou75@viajeseci.es
NOTE : Received : from viajeseci.es (unknown [222.222.219.154])
Phishing analysis :
CLICK : information.doc
OPEN : http://be-tiger.com/wp-content/sg.php
RESULT : Phishing was removed
Report-ID: *@* 21/04/2017 (Phishing attempt)
Dear Driver,
This is the automatic statement of the Parking Service.
Road cameras have recorded the limit exceeding of your vehicle. Therefore, you will have to pay the applicable fine.
--------------------------------------------------------------------------- ---
So as to successfully complete the payment, you will have to finalize the invoice on the official website.
Your Fine Invoice ID is VL05U
Please submit it here: pa rking-services.us
--------------------------------------------------------------------------- ---
Then, you will have all essential details to execute the payment.
You have one day to document the fine. Else, significant charges may apply.
Please do not reply to this message.
------
Kindest Regards,
Parking Service
Email analysis :
NOTE : oybi6@wwpinc.com
NOTE : User-Agent : Mozilla/5.0 (Windows; U; Windows NT 5.1;
NOTE : en-GB; rv:1.8.0.14) Gecko/20071210 Thunderbird/1.5.0.14
NOTE : client-ip=202.55.69.138;
Phishing analysis :
CLICK : pa rking-services.us
OPEN : http://www.wik.be/backend/modules/settings/c056bc1304.html
RESULT : Phishing attempt
This is the automatic statement of the Parking Service.
Road cameras have recorded the limit exceeding of your vehicle. Therefore, you will have to pay the applicable fine.
--------------------------------------------------------------------------- ---
So as to successfully complete the payment, you will have to finalize the invoice on the official website.
Your Fine Invoice ID is VL05U
Please submit it here: pa rking-services.us
--------------------------------------------------------------------------- ---
Then, you will have all essential details to execute the payment.
You have one day to document the fine. Else, significant charges may apply.
Please do not reply to this message.
------
Kindest Regards,
Parking Service
Email analysis :
NOTE : oybi6@wwpinc.com
NOTE : User-Agent : Mozilla/5.0 (Windows; U; Windows NT 5.1;
NOTE : en-GB; rv:1.8.0.14) Gecko/20071210 Thunderbird/1.5.0.14
NOTE : client-ip=202.55.69.138;
Phishing analysis :
CLICK : pa rking-services.us
OPEN : http://www.wik.be/backend/modules/settings/c056bc1304.html
RESULT : Phishing attempt
Saturday, May 13, 2017
Need mnoey?Eaarn 50.000 per moonth.
###MAKE MONEY ON1|NE###
===EAARN 50.000 PER MONNTH===
1.You need 0nly email to regisster
2.Fluly automattic sytsem!NOTHING TO DO...
3.@bs0lutely passvie inc0me
http://www.wildstonesolution.com/wp-content/plugins/wordpress-seo/vendor/xrstf/composer-php52/lib/5bc10d79da.html
The title of the scam can also be : Need mooney?Eran 50.000 per moonth. with a different content
###MAAKE MONNEY ONLLNE###
===EAARN 50.000 PER MONTH===
1.You neeed only emmail to reg|$ter
2.Fuliy automatic ssytem!NOTHING TO DO...
3.Absolute1y passive lnc0me
http://www.ieee-papers.com/wp-content/themes/twentyseventeen/2159b211e2.html
Email analysis :
NOTE : mhurdsj@excite.it
NOTE : gfgrimaud@tjb-barre.com
NOTE : 202.150.50.14
NOTE : 113.186.177.167
Phishing analysis :
CLICK : http://www.wildstonesolution.com/wp-content/plugins/wordpress-seo/vendor/xrstf/composer-php52/lib/5bc10d79da.html
Result : Redirect to Google, the phishing was removed...
CLICK : http://www.ieee-papers.com/wp-content/themes/twentyseventeen/2159b211e2.html
RESULT : Redirect to Google, the phishing was removed
NOTE : Two wordpress websites were compromised to do this phishing.
===EAARN 50.000 PER MONNTH===
1.You need 0nly email to regisster
2.Fluly automattic sytsem!NOTHING TO DO...
3.@bs0lutely passvie inc0me
http://www.wildstonesolution.com/wp-content/plugins/wordpress-seo/vendor/xrstf/composer-php52/lib/5bc10d79da.html
The title of the scam can also be : Need mooney?Eran 50.000 per moonth. with a different content
###MAAKE MONNEY ONLLNE###
===EAARN 50.000 PER MONTH===
1.You neeed only emmail to reg|$ter
2.Fuliy automatic ssytem!NOTHING TO DO...
3.Absolute1y passive lnc0me
http://www.ieee-papers.com/wp-content/themes/twentyseventeen/2159b211e2.html
Email analysis :
NOTE : mhurdsj@excite.it
NOTE : gfgrimaud@tjb-barre.com
NOTE : 202.150.50.14
NOTE : 113.186.177.167
Phishing analysis :
CLICK : http://www.wildstonesolution.com/wp-content/plugins/wordpress-seo/vendor/xrstf/composer-php52/lib/5bc10d79da.html
Result : Redirect to Google, the phishing was removed...
CLICK : http://www.ieee-papers.com/wp-content/themes/twentyseventeen/2159b211e2.html
RESULT : Redirect to Google, the phishing was removed
NOTE : Two wordpress websites were compromised to do this phishing.
Friday, May 12, 2017
Update Your Account Information Now !! (PayPal Phishing Attempt)
PayPal
Warning : Account Issue !
Your account is limited untill you update your information because some one requested acces to your account, here is the infos :
Location : Russia
IP adress : 176.96.80.140
Navigator : Mozilla Firefox 48.0 on Windows
The restore the access to your account please click on the link below :
Update My Account
This is an email sent automatically. Please do not reply to this letter, because the e-mail address is only configured to send but not to receive e-mails.
Copyright © 2017 All rights reserved.
Phishing screenshot :
Email analysis :
NOTE : morag@g-p-t.co.uk
NOTE : Received : from RDT.spectra.local (unknown [80.229.37.167])
NOTE : by cust-smtp-auth2.fasthosts.net.uk (Postfix)
NOTE : client-ip=213.171.216.60;
Phishing analysis :
CLICK : Update my Account
OPEN : http://sadagatismayilova.com/update-your-account-information-now/myaccount/
SCREENSHOT :
NOTE : Phishing was removed.
Warning : Account Issue !
Your account is limited untill you update your information because some one requested acces to your account, here is the infos :
Location : Russia
IP adress : 176.96.80.140
Navigator : Mozilla Firefox 48.0 on Windows
The restore the access to your account please click on the link below :
Update My Account
This is an email sent automatically. Please do not reply to this letter, because the e-mail address is only configured to send but not to receive e-mails.
Copyright © 2017 All rights reserved.
Phishing screenshot :
Email analysis :
NOTE : morag@g-p-t.co.uk
NOTE : Received : from RDT.spectra.local (unknown [80.229.37.167])
NOTE : by cust-smtp-auth2.fasthosts.net.uk (Postfix)
NOTE : client-ip=213.171.216.60;
Phishing analysis :
CLICK : Update my Account
OPEN : http://sadagatismayilova.com/update-your-account-information-now/myaccount/
SCREENSHOT :
NOTE : Phishing was removed.
Thursday, April 27, 2017
Crédit Mutuel de Bretagne
Bonjour,
Nous tenons de vous informer que vous avez un nouveau message.
Pour consulter votre boite de messagerie cliquez sur le lien ci-dessous :
Consulter la boite de messagerie
Cordialement,
Laurent Biojoux,
Directeur de la Relation Clients
Crédit Mutuel de Bretagne
Veuillez ne pas répondre à cet email car les messages reçus à cette adresse ne sont pas lus. Pour
nous contacter, connectez-vous à votre compte et cliquez sur Contact en bas de n'importe quelle page.
Email analysis :
NOTE : tracey.lahey@sympatico.ca
NOTE : cmb@contact.com
NOTE : Cmm-Sending-Ip : 184.150.200.79
Phishing analysis :
CLICK : Consulter la boite de messagerie
OPEN : https://tinyurl.com/k96mlop
Nous tenons de vous informer que vous avez un nouveau message.
Pour consulter votre boite de messagerie cliquez sur le lien ci-dessous :
Consulter la boite de messagerie
Cordialement,
Laurent Biojoux,
Directeur de la Relation Clients
Crédit Mutuel de Bretagne
Veuillez ne pas répondre à cet email car les messages reçus à cette adresse ne sont pas lus. Pour
nous contacter, connectez-vous à votre compte et cliquez sur Contact en bas de n'importe quelle page.
Email analysis :
NOTE : tracey.lahey@sympatico.ca
NOTE : cmb@contact.com
NOTE : Cmm-Sending-Ip : 184.150.200.79
Phishing analysis :
CLICK : Consulter la boite de messagerie
OPEN : https://tinyurl.com/k96mlop
AUTOMATIC USPS statement: your package has been postponed
This is an automatic message: you are obliged to read this letter to accept
the order.
Please, use the link seen down below to contact the USPS support team.
http://www.stbishoy.org/wp-content/b4d47c6405.html
Thanks and best regards.
Takeisha Wernecke - USPS Senior Station Manager.
Email analysis :
NOTE : wo56816421@occhristian.pvt.k12.ia.us
NOTE : USPS Priority
NOTE : Received : from occhristian.pvt.k12.ia.us (unknown [186.151.239.161])
NOTE : User-Agent : Opera Mail/10.62 (Win32)
NOTE : 186.151.239.161
Phishing analysis :
CLICK : http://www.stbishoy.org/wp-content/b4d47c6405.html
OPEN : http://www.stbishoy.org/wp-content/b4d47c6405.html
REDIRECT : http://servisedelivery.com/bot14/lgen.php
RESULT : Phishing is unresponsive...
Stbishoy.org analysis :
Registrant Email: stbishoy.org@proxy.dreamhost.com
Updated Date: 2016-11-01T18:00:21
Creation Date: 2009-08-02T04:33:23
Registry Expiry Date: 2017-08-02T04:33:23
Servisedelivery.com analysis :
Updated Date: 2017-04-24T17:04:10
Creation Date: 2017-04-24T00:00:00
Registrar Registration Expiration Date: 2018-04-24T00:00:00
Registrar Abuse Contact Email: abuse@bizcn.com
Registrant Name: Wuxi Yilian LLC
Registrant Organization: Wuxi Yilian LLC
Registrant Street: No.1001 Anling Road
Registrant City: Xiamen
Registrant State/Province: Fujian
Registrant Postal Code: 361008
Registrant Country: cn
Registrant Phone: +86.5922577888
Registrant Fax: +86.5922179606
Registrant Email: whoisprivacyprotect@whoisservices.cn
the order.
Please, use the link seen down below to contact the USPS support team.
http://www.stbishoy.org/wp-content/b4d47c6405.html
Thanks and best regards.
Takeisha Wernecke - USPS Senior Station Manager.
Email analysis :
NOTE : wo56816421@occhristian.pvt.k12.ia.us
NOTE : USPS Priority
NOTE : Received : from occhristian.pvt.k12.ia.us (unknown [186.151.239.161])
NOTE : User-Agent : Opera Mail/10.62 (Win32)
NOTE : 186.151.239.161
Phishing analysis :
CLICK : http://www.stbishoy.org/wp-content/b4d47c6405.html
OPEN : http://www.stbishoy.org/wp-content/b4d47c6405.html
REDIRECT : http://servisedelivery.com/bot14/lgen.php
RESULT : Phishing is unresponsive...
Stbishoy.org analysis :
Registrant Email: stbishoy.org@proxy.dreamhost.com
Updated Date: 2016-11-01T18:00:21
Creation Date: 2009-08-02T04:33:23
Registry Expiry Date: 2017-08-02T04:33:23
Servisedelivery.com analysis :
Updated Date: 2017-04-24T17:04:10
Creation Date: 2017-04-24T00:00:00
Registrar Registration Expiration Date: 2018-04-24T00:00:00
Registrar Abuse Contact Email: abuse@bizcn.com
Registrant Name: Wuxi Yilian LLC
Registrant Organization: Wuxi Yilian LLC
Registrant Street: No.1001 Anling Road
Registrant City: Xiamen
Registrant State/Province: Fujian
Registrant Postal Code: 361008
Registrant Country: cn
Registrant Phone: +86.5922577888
Registrant Fax: +86.5922179606
Registrant Email: whoisprivacyprotect@whoisservices.cn
Monday, April 24, 2017
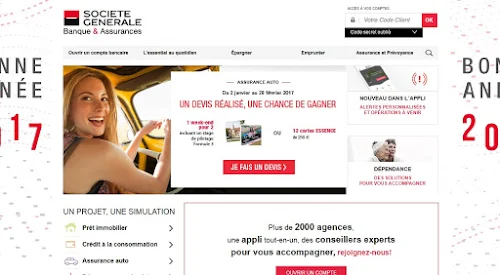
Vous avez de nouveau message ( Phishing Société Générale )
Cher(e) Client(e),
Votre conseiller vous informe que vous avez reçu un message important
conçernant votrecPass ,
eAccèsuàxvosxcomptes
Cordialement
Société Générale
sg
Email analysis :
NOTE : X-Php-Originating-Script : 0:njd.php
NOTE : e@atosucire.com
NOTE : Received : by batidocs.fr (Postfix, from userid 33)
NOTE : Received : from batidocs.fr ([46.101.97.198])
Phishing analysis :
CLICK : eAccèsuàxvosxcomptes
OPEN : http://ecodebredpasrapel.com/votrecode
REDIRECT : http://www.drivegeelong.com.au/journal/url/njd
RESULT : Phishing attempt...
Affected services :
NOTE : e@atosucire.com (Spoofed email.)
NOTE : batidocs.fr (46.101.97.198) (Relaying the phishing email.)
NOTE : ecodebredpasrapel.com (Hosting the redirect to the phishing.)
NOTE : drivegeelong.com.au (Hosting the phishing.)
NOTE : Société Générale (Victim.)
Votre conseiller vous informe que vous avez reçu un message important
conçernant votrecPass ,
eAccèsuàxvosxcomptes
Cordialement
Société Générale
sg
Email analysis :
NOTE : X-Php-Originating-Script : 0:njd.php
NOTE : e@atosucire.com
NOTE : Received : by batidocs.fr (Postfix, from userid 33)
NOTE : Received : from batidocs.fr ([46.101.97.198])
Phishing analysis :
CLICK : eAccèsuàxvosxcomptes
OPEN : http://ecodebredpasrapel.com/votrecode
REDIRECT : http://www.drivegeelong.com.au/journal/url/njd
RESULT : Phishing attempt...
Affected services :
NOTE : e@atosucire.com (Spoofed email.)
NOTE : batidocs.fr (46.101.97.198) (Relaying the phishing email.)
NOTE : ecodebredpasrapel.com (Hosting the redirect to the phishing.)
NOTE : drivegeelong.com.au (Hosting the phishing.)
NOTE : Société Générale (Victim.)
Banco Santander (Brasil) S.A. | Evite Bloqueio de sua conta (*) (Phishing Attempt)
Banco Santander S.A.
Prezado(a) Cliente,
Comunicamos que seus dados cadastrais encontram-se desatualizados em nosso sistema.Para que você possa desfrutar dos benefícios com comodidade e segurança, pedimos que você efetue a Atualização Cadastral de Segurança imposta pelo nosso sistema.
Este procedimento deve ser efetuado, evitando o bloqueio aos canais Santander tais como Telefone, Internet Banking e Caixas Eletrônicos.
Para evitar a suspensão automática desses serviços, habilite suas atualizações clicando no botão abaixo.
Este recurso só é ativado se você aceitar, e é atualizado a partir de servidores certificados..
Deseja confirmar suas definições de segurança?
Confirmar
Banco Santander (Brasil) S.A. CNPJ: 90.400.888/0001-42 Avenida Presidente Juscelino Kubitschek, 2041 e 2235 - Bloco A, Vila Olímpia, São Paulo/SP - CEP 04543-011
Screenshot of the phishing :
Email analysis :
NOTE : Received : by ip-160-153-226-153.ip.secureserver.net
NOTE : (Postfix, from userid 33)
NOTE : 160.153.226.184
NOTE : X-Mailer : Microsoft Office Outlook, Build 17.551210
NOTE : X-Mailer : iGMail [www.ig.com.br]
Phishing analysis :
CLICK : Confirmar
OPEN : http://ip-160-153-229-233.ip.secureserver.net/cadastro/*
RESULT : Phishing is unresponsive...
Prezado(a) Cliente,
Comunicamos que seus dados cadastrais encontram-se desatualizados em nosso sistema.Para que você possa desfrutar dos benefícios com comodidade e segurança, pedimos que você efetue a Atualização Cadastral de Segurança imposta pelo nosso sistema.
Este procedimento deve ser efetuado, evitando o bloqueio aos canais Santander tais como Telefone, Internet Banking e Caixas Eletrônicos.
Para evitar a suspensão automática desses serviços, habilite suas atualizações clicando no botão abaixo.
Este recurso só é ativado se você aceitar, e é atualizado a partir de servidores certificados..
Deseja confirmar suas definições de segurança?
Confirmar
Banco Santander (Brasil) S.A. CNPJ: 90.400.888/0001-42 Avenida Presidente Juscelino Kubitschek, 2041 e 2235 - Bloco A, Vila Olímpia, São Paulo/SP - CEP 04543-011
Screenshot of the phishing :
Email analysis :
NOTE : Received : by ip-160-153-226-153.ip.secureserver.net
NOTE : (Postfix, from userid 33)
NOTE : 160.153.226.184
NOTE : X-Mailer : Microsoft Office Outlook, Build 17.551210
NOTE : X-Mailer : iGMail [www.ig.com.br]
Phishing analysis :
CLICK : Confirmar
OPEN : http://ip-160-153-229-233.ip.secureserver.net/cadastro/*
RESULT : Phishing is unresponsive...
Tuesday, April 11, 2017
Alertes (Phishing Société Générale)
Cher(e) Client(e)
AfinJdeJprévenirJl'utilisationJfrauduleuseJdesJcartesJbancairesJsurJinternet,
SociétéJGénéraleJestJdotéeJd'unJdispositifJdeJcontroleJdesJprélèvements.CeJservicejj
estJentierementJgratuitJNotreJsystemeJaJdetecteJqueJvousJn'avezJpasJactivéJPasse sécurité.
PourJactivéJleJPasseJsécurité, VeuillerJcliquez sur leJlienJci-dessous :
Cliquez ici
NousJvousJremercionsJdeJvotreJconfiance.
Cordialement,
DirecteurJdeJlaJrelationJclients.
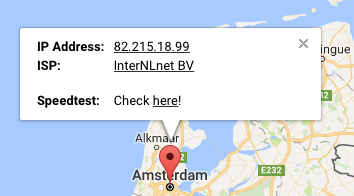
Phishing screenshot :
Email analysis :
NOTE : jan.v.d.kamp@versatel.nl
NOTE : Cmm-Sending-Ip : 82.215.18.99
NOTE : Received : by webmail01.zonnet.isp-net.nl (Postfix, from userid 33)
Phishing analysis :
CLICK : Cliquez ici
OPEN : http://www.asociacioncar.com/adm
REDIRECT : http://tabonm79.beget.tech/googl/sg2017/*/
NOTE : ENTER FAKE PASSWORD AND USER
REDIRECT : http://tabonm79.beget.tech/googl/sg2017/*/dcr-web/
Affected services :
NOTE : Fietsenwinkel.nl (Relaying the phishing email.)
NOTE : asociacioncar.com (Hosting the redirect to the phishing.)
NOTE : tabonm79.beget.tech (Hosting the phishing.)
NOTE : beget.tech (Hosting the phishing page.)
NOTE : Société Générale (Victim)
AfinJdeJprévenirJl'utilisationJfrauduleuseJdesJcartesJbancairesJsurJinternet,
SociétéJGénéraleJestJdotéeJd'unJdispositifJdeJcontroleJdesJprélèvements.CeJservicejj
estJentierementJgratuitJNotreJsystemeJaJdetecteJqueJvousJn'avezJpasJactivéJPasse sécurité.
PourJactivéJleJPasseJsécurité, VeuillerJcliquez sur leJlienJci-dessous :
Cliquez ici
NousJvousJremercionsJdeJvotreJconfiance.
Cordialement,
DirecteurJdeJlaJrelationJclients.
Phishing screenshot :
Email analysis :
NOTE : jan.v.d.kamp@versatel.nl
NOTE : Cmm-Sending-Ip : 82.215.18.99
NOTE : Received : by webmail01.zonnet.isp-net.nl (Postfix, from userid 33)
Phishing analysis :
CLICK : Cliquez ici
OPEN : http://www.asociacioncar.com/adm
REDIRECT : http://tabonm79.beget.tech/googl/sg2017/*/
NOTE : ENTER FAKE PASSWORD AND USER
REDIRECT : http://tabonm79.beget.tech/googl/sg2017/*/dcr-web/
Affected services :
NOTE : Fietsenwinkel.nl (Relaying the phishing email.)
NOTE : asociacioncar.com (Hosting the redirect to the phishing.)
NOTE : tabonm79.beget.tech (Hosting the phishing.)
NOTE : beget.tech (Hosting the phishing page.)
NOTE : Société Générale (Victim)
Wednesday, April 5, 2017
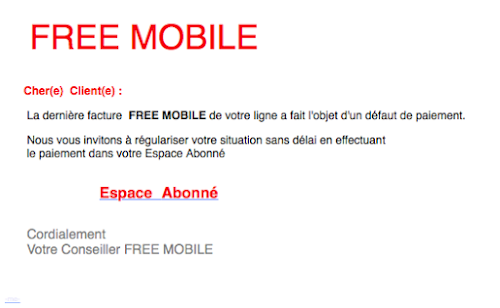
Service CIient - Nouveau message
FREE MOBILE
Cher(e)aClient(e) :
La dernière facture FREE MOBILE de votre ligne a fait l'objet d'un défaut de paiement.
Nous vous invitons à régulariser votre situation sans délai en effectuant
le paiement dans votre Espace Abonné
EspaceoAbonné
Cordialement
Votre ConseillertFREEtMOBILE
-me-
Email analysis :
NOTE : FREE.MOBlLE@senior-meilleuresoffres.net
NOTE : X-Php-Originating-Script : 0:ark.php
NOTE : Received : by news.monoprix.fr (Postfix, from userid 33)
NOTE : ark@news.monoprix.fr
Phishing screenshot :
Phishing analysis :
CLICK : EspaceoAbonné
OPEN : http://www.libertycoingalleries.com/var
REDIRECT : http://tee-managerdesigner.com/vqmod/css/faicon/28452fa1dfa2fa1778723ec9ae1bd38f/
SCREENSHOT :
Affected services :
NOTE : news.monoprix.fr (Relaying the phishing email.)
NOTE : libertycoingalleries.com (Hosting the redirect to the phishing.)
NOTE : tee-managerdesigner.com (Hosting the phishing.)
NOTE : hostgator.com (Hosting the phishing page.)
NOTE : Free (Victim)
Cher(e)aClient(e) :
La dernière facture FREE MOBILE de votre ligne a fait l'objet d'un défaut de paiement.
Nous vous invitons à régulariser votre situation sans délai en effectuant
le paiement dans votre Espace Abonné
EspaceoAbonné
Cordialement
Votre ConseillertFREEtMOBILE
-me-
Email analysis :
NOTE : FREE.MOBlLE@senior-meilleuresoffres.net
NOTE : X-Php-Originating-Script : 0:ark.php
NOTE : Received : by news.monoprix.fr (Postfix, from userid 33)
NOTE : ark@news.monoprix.fr
Phishing screenshot :
Phishing analysis :
CLICK : EspaceoAbonné
OPEN : http://www.libertycoingalleries.com/var
REDIRECT : http://tee-managerdesigner.com/vqmod/css/faicon/28452fa1dfa2fa1778723ec9ae1bd38f/
SCREENSHOT :
Affected services :
NOTE : news.monoprix.fr (Relaying the phishing email.)
NOTE : libertycoingalleries.com (Hosting the redirect to the phishing.)
NOTE : tee-managerdesigner.com (Hosting the phishing.)
NOTE : hostgator.com (Hosting the phishing page.)
NOTE : Free (Victim)
Enc:DHL delivery Cust. Ref: 539000135
dhllogo.gif
Dear *@*.*,
A Package is coming your way through DHL.
Kindly confirm if the address is correct and you can also track your Package till it gets to your doorstep.
Track Your Package
DHL Worldwide Delivery ©.
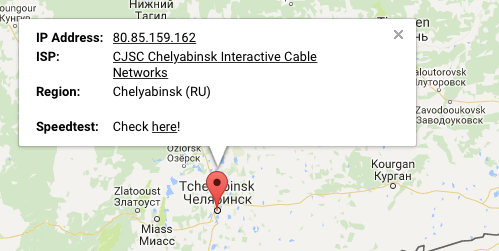
Email analysis :
NOTE : inbox@vaemail.ru
NOTE : Received : from vaemail.ru (vaemail.ru. [80.85.159.162])
NOTE : client-ip=80.85.159.162;
Phishing analysis :
CLICK : Track Your Package
OPEN : http://thedanbury.com/dhl/DHLAUTO/track/dhl.php?email=*
RESULT : Phishing was removed...
Dear *@*.*,
A Package is coming your way through DHL.
Kindly confirm if the address is correct and you can also track your Package till it gets to your doorstep.
Track Your Package
DHL Worldwide Delivery ©.
Email analysis :
NOTE : inbox@vaemail.ru
NOTE : Received : from vaemail.ru (vaemail.ru. [80.85.159.162])
NOTE : client-ip=80.85.159.162;
Phishing analysis :
CLICK : Track Your Package
OPEN : http://thedanbury.com/dhl/DHLAUTO/track/dhl.php?email=*
RESULT : Phishing was removed...
Thursday, March 9, 2017
Notification : securite (Phishing Société Générale)
Bonjour,
Afin de prévenir l'utilisation frauduleuse des cartes bancaires sur Internet, Société Générale
est dotée d'un dispositif de controle
Ce service est entierement gratuit Notre systeme a detecte que vous n'avez pas active Pass sécurité
.aCliquez-ici
Nous vous remercions de votre confiance.
Cordialement
Directeur de la relation clients
Société-Générale
Vueling App
Descargar
Ayuda
Ayuda
Pregúntanos
Reservas
Reservas
902 808 022
Añade vueling@news.vueling.com a tu libreta de direcciones y asegúrate de recibir todas nuestras comunicaciones.
Deseamos que este mensaje haya resultado de tu interés. No obstante, si prefieres no recibir más comunicaciones de este tipo, no dudes en comunicárnoslo aquí.
El proceso de tramitación de la baja puede tardar algunos días, con lo cual es posible que puedas recibir esta comunicación hasta que se realice el cambio pertinente.
Este mensaje ha sido enviado por un sistema automático. Por favor, no respondas este email directamente.
Facebook Twitter My Vueling City Instagram Youtube
©2017 Vueling Airlines SA
Phishing screenshot :
Email analysis :
NOTE : Received : from fandevoyages.fr ([139.59.64.182])
NOTE : X-Php-Originating-Script : 0:l3nan.php
NOTE : info@nl.fandevoyages.fr
Phishing analysis :
CLICK : Cliquez-ici
OPEN : http://forum.onlydutch.com/lazem.html
REDIRECT : http://stroi-servicenn.ru/wp-content/upgrade/account/sg/*/
SCREENSHOT :
NOTE : TEST CODE
SCREENSHOT :
NOTE : EXPLOITED WEBSITE RELAYING THE PHISHING : http://stroi-servicenn.ru
SCREENSHOT :
Afin de prévenir l'utilisation frauduleuse des cartes bancaires sur Internet, Société Générale
est dotée d'un dispositif de controle
Ce service est entierement gratuit Notre systeme a detecte que vous n'avez pas active Pass sécurité
.aCliquez-ici
Nous vous remercions de votre confiance.
Cordialement
Directeur de la relation clients
Société-Générale
Vueling App
Descargar
Ayuda
Ayuda
Pregúntanos
Reservas
Reservas
902 808 022
Añade vueling@news.vueling.com a tu libreta de direcciones y asegúrate de recibir todas nuestras comunicaciones.
Deseamos que este mensaje haya resultado de tu interés. No obstante, si prefieres no recibir más comunicaciones de este tipo, no dudes en comunicárnoslo aquí.
El proceso de tramitación de la baja puede tardar algunos días, con lo cual es posible que puedas recibir esta comunicación hasta que se realice el cambio pertinente.
Este mensaje ha sido enviado por un sistema automático. Por favor, no respondas este email directamente.
Facebook Twitter My Vueling City Instagram Youtube
©2017 Vueling Airlines SA
Phishing screenshot :
Email analysis :
NOTE : Received : from fandevoyages.fr ([139.59.64.182])
NOTE : X-Php-Originating-Script : 0:l3nan.php
NOTE : info@nl.fandevoyages.fr
Phishing analysis :
CLICK : Cliquez-ici
OPEN : http://forum.onlydutch.com/lazem.html
REDIRECT : http://stroi-servicenn.ru/wp-content/upgrade/account/sg/*/
SCREENSHOT :
NOTE : TEST CODE
SCREENSHOT :
NOTE : EXPLOITED WEBSITE RELAYING THE PHISHING : http://stroi-servicenn.ru
SCREENSHOT :
Saturday, February 25, 2017
Your iTunes ID (Phishing attempt)
Update your account when you're ready.
We suspect that someone is trying to use your account. When you're ready, click the link below to update your account information. For your safety your account has been temporarily locked.
https://appleid.apple.com/IDMSWebAuth/login.html?appIdKey=fgd55eeklw56q96w qq64.
Case ID: 662498345
This link will expire after 24 hours.
Sincerely,
Apple Support
Get help online
Visit Apple Support to learn more about your product, download software updates, and much more.
Join the conversation
Find and share solutions with Apple users around the world.
copyright 2016 Apple Inc.
All Rights Reserved / Privacy Policy / Support / Give us feedback
On behalf of Apple Distribution International
Phishing screenshot :
Email analysis :
NOTE : no-reply@services-apple.com
NOTE : X-Php-Originating-Script : 33:01.php(4) : eval()'d code
NOTE : Received : by cptweb02 (Postfix, from userid 33)
NOTE : CPT WEBSERVER
NOTE : client-ip=77.95.37.80;
Phishing analysis :
CLICK : https://appleid.apple.com/IDMSWebAuth/login.html?appIdKey=fgd55eeklw56q96w qq64.
OPEN : Link wasn't activated...
RESULT : Phishing attempt.
We suspect that someone is trying to use your account. When you're ready, click the link below to update your account information. For your safety your account has been temporarily locked.
https://appleid.apple.com/IDMSWebAuth/login.html?appIdKey=fgd55eeklw56q96w qq64.
Case ID: 662498345
This link will expire after 24 hours.
Sincerely,
Apple Support
Get help online
Visit Apple Support to learn more about your product, download software updates, and much more.
Join the conversation
Find and share solutions with Apple users around the world.
copyright 2016 Apple Inc.
All Rights Reserved / Privacy Policy / Support / Give us feedback
On behalf of Apple Distribution International
Phishing screenshot :
Email analysis :
NOTE : no-reply@services-apple.com
NOTE : X-Php-Originating-Script : 33:01.php(4) : eval()'d code
NOTE : Received : by cptweb02 (Postfix, from userid 33)
NOTE : CPT WEBSERVER
NOTE : client-ip=77.95.37.80;
Phishing analysis :
CLICK : https://appleid.apple.com/IDMSWebAuth/login.html?appIdKey=fgd55eeklw56q96w qq64.
OPEN : Link wasn't activated...
RESULT : Phishing attempt.
Friday, February 17, 2017
Important Message from PayPal ! (PayPal Phishing)
Your PayPaI Account logged form another device !
If you are seeing the messages this means that your account has been visited from an another place given below :
IP : 176.97.103.90
Country : Ukrania
Ville : Odessa
As a security measure, your account has been Iimited.
Case id : PP-801-707-057
Don't worry, you will be able to get your account back just after finishing this steps.
To continue follow this link : :Click Here✔
Notice :If you receive this email in the SPAM folder,click on "Not Spam" button to fix it
Email analysis :
NOTE : Received : from cptweb02 ([77.95.37.80])
NOTE : PayPal@service.com
Phishing analysis :
CLICK : Click Here✔
OPEN : https://jasper.nswebhost.com/~brainrec/paypal-support/
REDIRECT : https://jasper.nswebhost.com/~brainrec/paypal-support/paypal/login.php
SCREENSHOT :
If you are seeing the messages this means that your account has been visited from an another place given below :
IP : 176.97.103.90
Country : Ukrania
Ville : Odessa
As a security measure, your account has been Iimited.
Case id : PP-801-707-057
Don't worry, you will be able to get your account back just after finishing this steps.
To continue follow this link : :Click Here✔
Notice :If you receive this email in the SPAM folder,click on "Not Spam" button to fix it
Email analysis :
NOTE : Received : from cptweb02 ([77.95.37.80])
NOTE : PayPal@service.com
Phishing analysis :
CLICK : Click Here✔
OPEN : https://jasper.nswebhost.com/~brainrec/paypal-support/
REDIRECT : https://jasper.nswebhost.com/~brainrec/paypal-support/paypal/login.php
SCREENSHOT :
Subscribe to:
Posts (Atom)